Crystal Eye NDR
Network Detection and Response
Purpose-Built Threat Defence Beyond AI
Ready to take your threat defence to the next level?
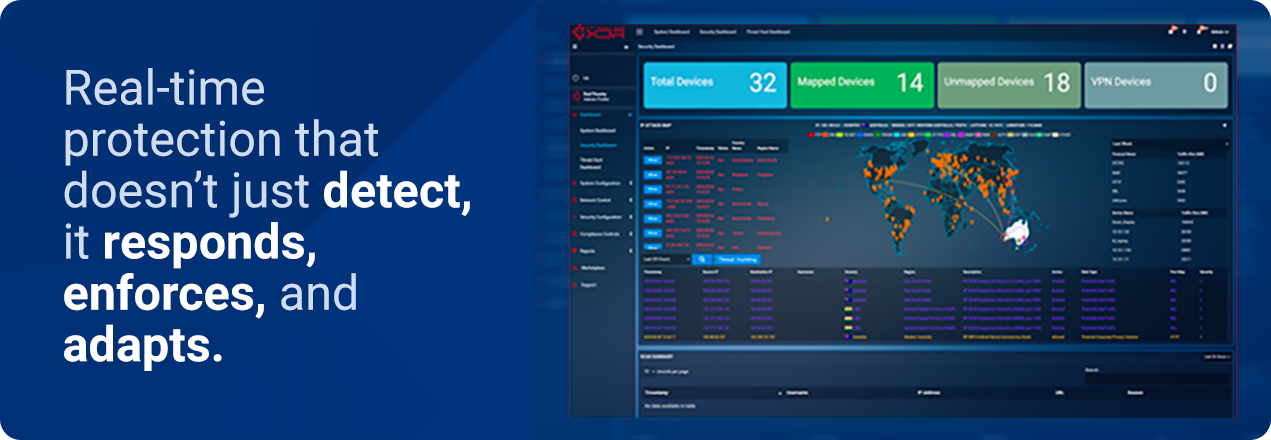
Cyberattacks are on the rise, so it is more important than ever to have a reliable security system that can detect and respond to threats in real-time. Crystal Eye Network Detection and Response solution is designed to do just that.
Crystal Eye NDR is more than just another network detection solution. Developed by Red Piranha, a true cybersecurity company, it ties in with our Threat Detection, Investigation, and Response (TDIR) engine designed for security professionals who demand more than buzzwords.
Unlike traditional tools that lean solely on AI, EDR or other standalone solutions, Crystal Eye NDR combines human-machine teaming, cyber threat intelligence, and actionable policy enforcement into a fully integrated security fabric. This provides a full TDIR lifecycle capturing almost all known threats.
Why Crystal Eye NDR?
- Real-time threat detection and response
- No-retainer, on-demand human threat hunting
- Integrated policy enforcement across environments
- Enterprise-ready, multi-tenanted design
- Backed by a trusted Australian cybersecurity company
- Augmented Security Operation Center
- 18+ months log retention
Go Beyond Detection
Crystal Eye NDR isn’t just AI. It’s actionable intelligence, expert response, and enforced protection deployed at scale.