
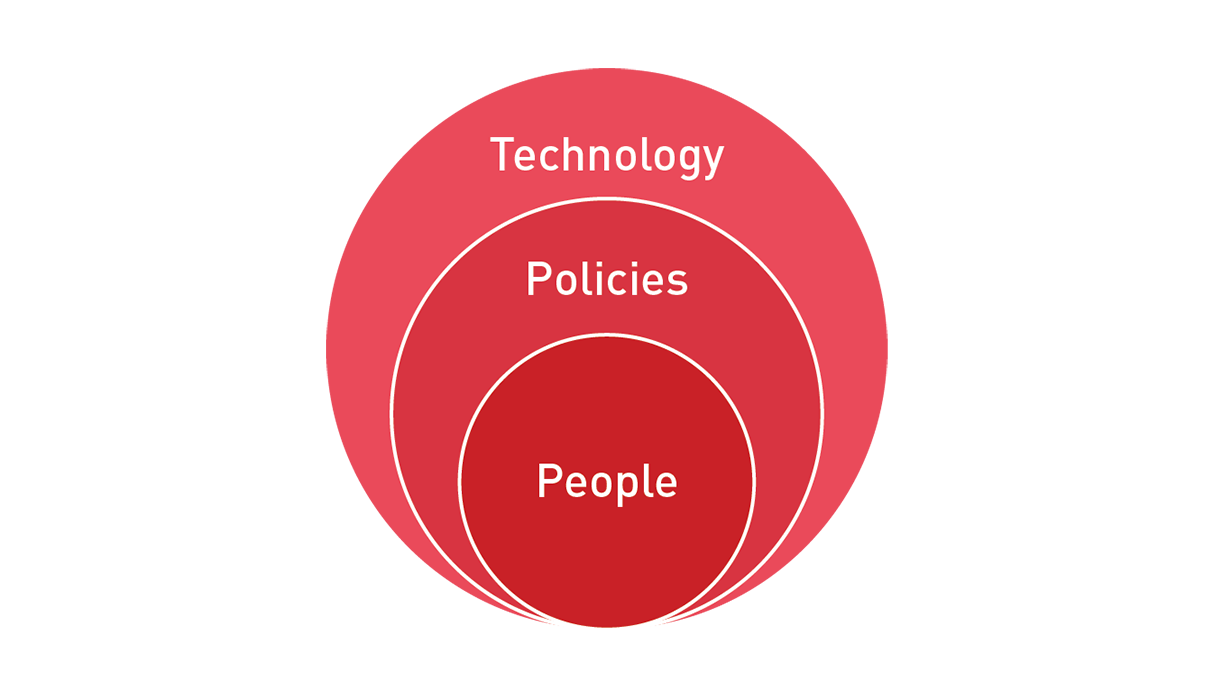
People, Processes & Technology are 3 key pillars of your Information Security Management System (ISMS).
Every day, you might use a mobile device to make calls, send text messages, post articles on social media platforms, and access information on the web.
It's also likely you use a laptop or tablet to communicate, perform work, store work files, video conference or watch recorded files. Your personal and work data are recorded on these devices in real time. These files may be backed up in local as well as offsite infrastructure. Each new device doesn’t just drive traffic; it also dramatically expands the network attack surface - increasing the opportunity for cybercriminals to leverage sophisticated methods to exploit these opportunities. As a result, we are seeing a rise in cybercrime, and cybersecurity incidents that exploit data found on your devices, on-premises systems, as well as offsite cloud infrastructure.
The demand for digital protection on your network and storage infrastructure, particularly in the event of a data breach has increased exponentially due to the sheer number of attacks that organisations now face. In the first half of 2019 alone, major incidents in Australia such as the ANU, ACU, Landmark White and Westpac may have drawn the most media attention, but attacks against small and medium businesses that include data breaches, fund transfers, and intellectual property theft are no longer rare. And these security breaches are costing organisations millions of dollars.
It’s a common misconception that cybersecurity is all about technology (hardware and software). Technology is an integral part of cybersecurity, but on its own, it is not enough to protect you from many cyber threats. Practical and robust cybersecurity requires an information security management system (ISMS) built on three pillars – People, Processes and Technology.
You may have the technology in place, but if you don’t have proper processes and haven’t trained your staff on how to use this technology, then you create vulnerabilities.
Human error is known to account for a high percentage of all cyber-attacks.
The first action point with your people or employees is to educate and inoculate them from potential threats - helping them understand implications.
Implementing a basic cybersecurity training program could be the difference between maintaining a secure network and having a catastrophic breach.
Cybersecurity awareness training should be aimed at all people across the business to give them an essential understanding of how to keep the data and systems safe at all times. It starts with standard practices such as basic internet hygiene, usage of unauthorised USB storage, spotting a phishing attack and how to handle ransomware.
As a trusted partner, Red Piranha has an effective cybersecurity awareness training program, designed to enable everyone, regardless of their level of awareness, to be better equipped to identify potential threats.
Many organisations have processes in place, but how many people know what they are? For example, if your manager asked for your password to access your work systems would you give it? Would you hand over your personal details to a stranger? The answer to all of these questions should be NO if it’s not already clear.
Lack of processes or processes that are not enforced lead to vulnerabilities in your system. Think about hearing the fire alarm at work. Everyone knows they should immediately evacuate the building as quickly and safely as possible, but does everyone know what to do if they think their system has been breached? Failure to respond rapidly could lead to the damage becoming more severe.
This is where an Electronic Chief Information Security Officer (eCISO) service can help to develop a comprehensive strategy and implement an effective plan, to embed security consciousness across your entire organisation; minimise the attack surface of your network, and inoculate your people and infrastructure of potential threats. The right network security partner can help you to ensure that all your people and processes are security-oriented and compliant.
Regardless of the scale and size of your organisation, your people (staff awareness and training), processes (company policies) and technology (usage, encryption, data backup and security) should all be aligned to well-designed strategies and implementation plans. Failure to align and integrate your operations across all three pillars would likely lead to vulnerabilities in your organisation, and therefore high likelihood of disruption and theft of your most valuable asset – business data.

