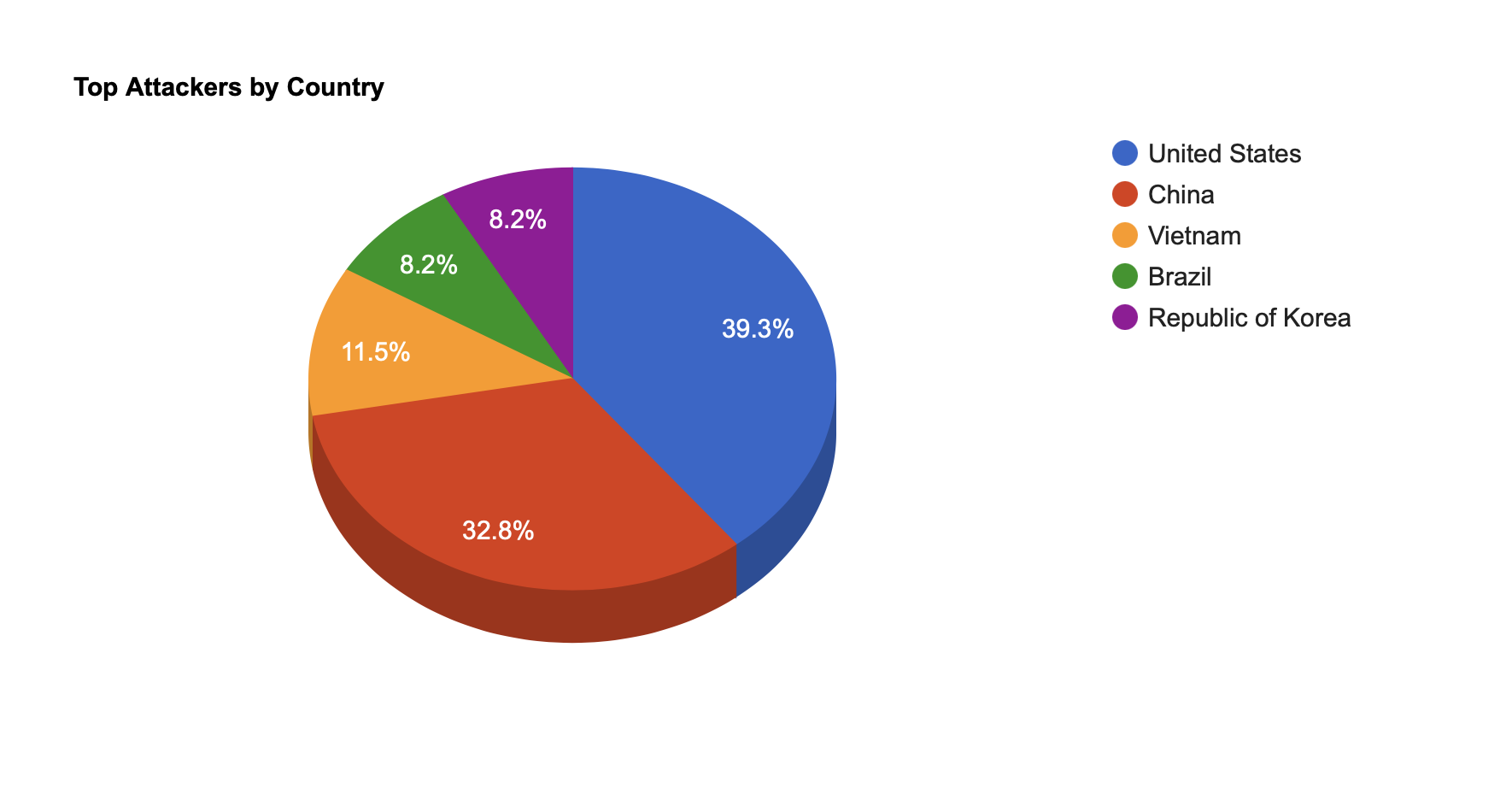
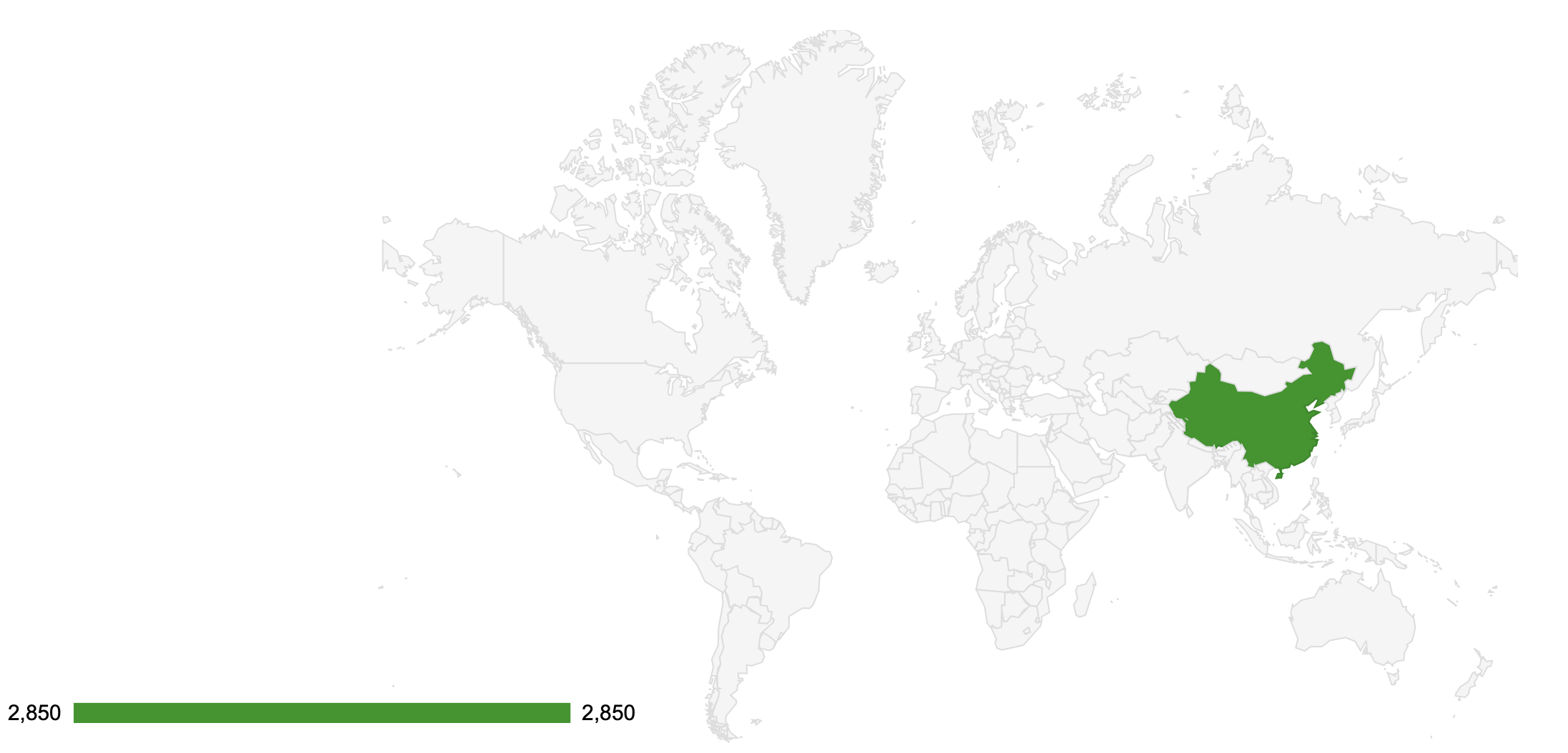
Top Attackers By Country
| China |
2850 |
71.00% |
| United States |
466 |
11.00% |
| Kenya |
156 |
3.00% |
| Iran |
105 |
2.00% |
| Panama |
80 |
2.00% |
| France |
62 |
1.00% |
| Canada |
58 |
1.00% |
| Uzbekistan |
42 |
1.00% |
| Russia |
40 |
1.00% |
| Philippines |
35 |
0% |
| Hong Kong |
19 |
0% |
| Germany |
16 |
0% |
| Singapore |
12 |
0% |
| Australia |
11 |
0% |
| India |
5 |
0% |
| Brazil |
5 |
0% |
| Bulgaria |
4 |
0% |
| Pakistan |
3 |
0% |
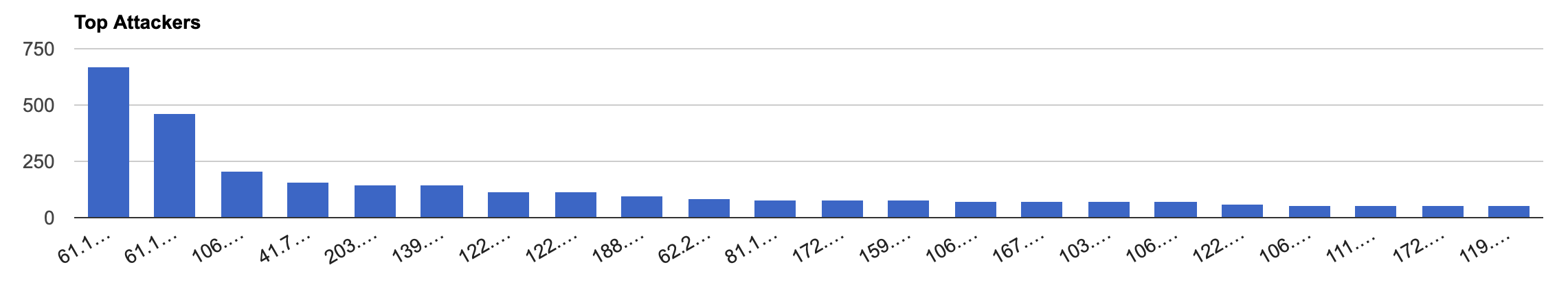
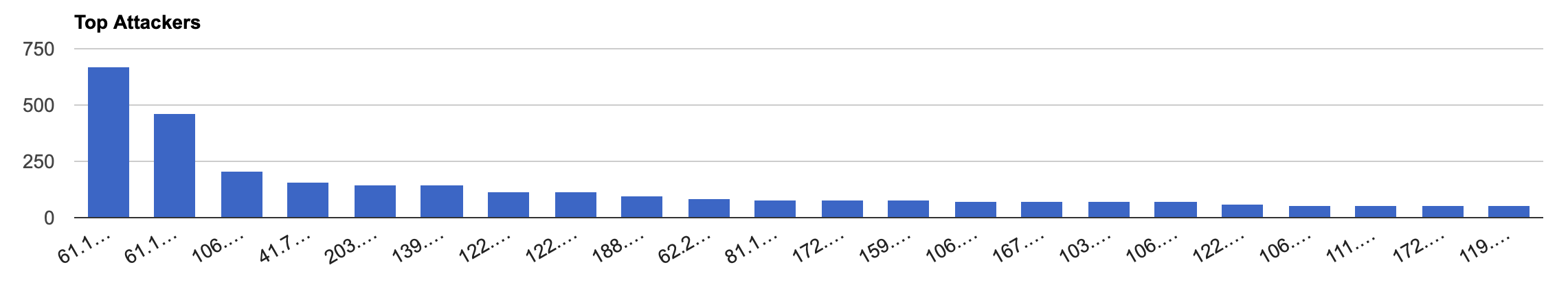
Top Attacking Hosts
| 61.177.173.20 |
673 |
| 61.177.173.4 |
463 |
| 106.52.105.178 |
206 |
| 41.76.175.165 |
156 |
| 203.195.205.202 |
146 |
| 139.219.6.159 |
145 |
| 122.51.100.145 |
117 |
| 122.51.52.154 |
116 |
| 188.0.240.178 |
100 |
| 62.234.6.147 |
84 |
| 81.17.16.110 |
78 |
| 172.81.251.217 |
78 |
| 159.89.82.134 |
77 |
| 106.55.147.115 |
76 |
| 167.172.194.231 |
76 |
| 103.192.253.218 |
72 |
| 106.13.52.192 |
72 |
| 122.51.96.57 |
64 |
| 106.53.236.114 |
53 |
| 111.177.20.50 |
53 |
| 172.93.40.245 |
52 |
| 119.45.242.149 |
52 |
Top Attackers
|
Top Network Attackers
| 4134 |
China |
CHINANET-BACKBONE No.31,Jin-rong Street, CN |
| 45090 |
China |
CNNIC-TENCENT-NET-AP Shenzhen Tencent Computer Systems Company Limited, CN |
| 37219 |
Kenya |
ICTA-, KE |
| 58593 |
China |
BLUECLOUD Shanghai Blue Cloud Technology Co.,Ltd, CN |
| 43754 |
Iran |
ASIATECH, IR |
| 51852 |
Switzerland |
PLI-AS, PA |
| 14061 |
United States |
DIGITALOCEAN-ASN, US |
| 4812 |
China |
CHINANET-SH-AP China Telecom (Group), CN |
| 38365 |
China |
BAIDU Beijing Baidu Netcom Science and Technology Co., Ltd., CN |
| 25820 |
Canada |
IT7NET, CA |
|
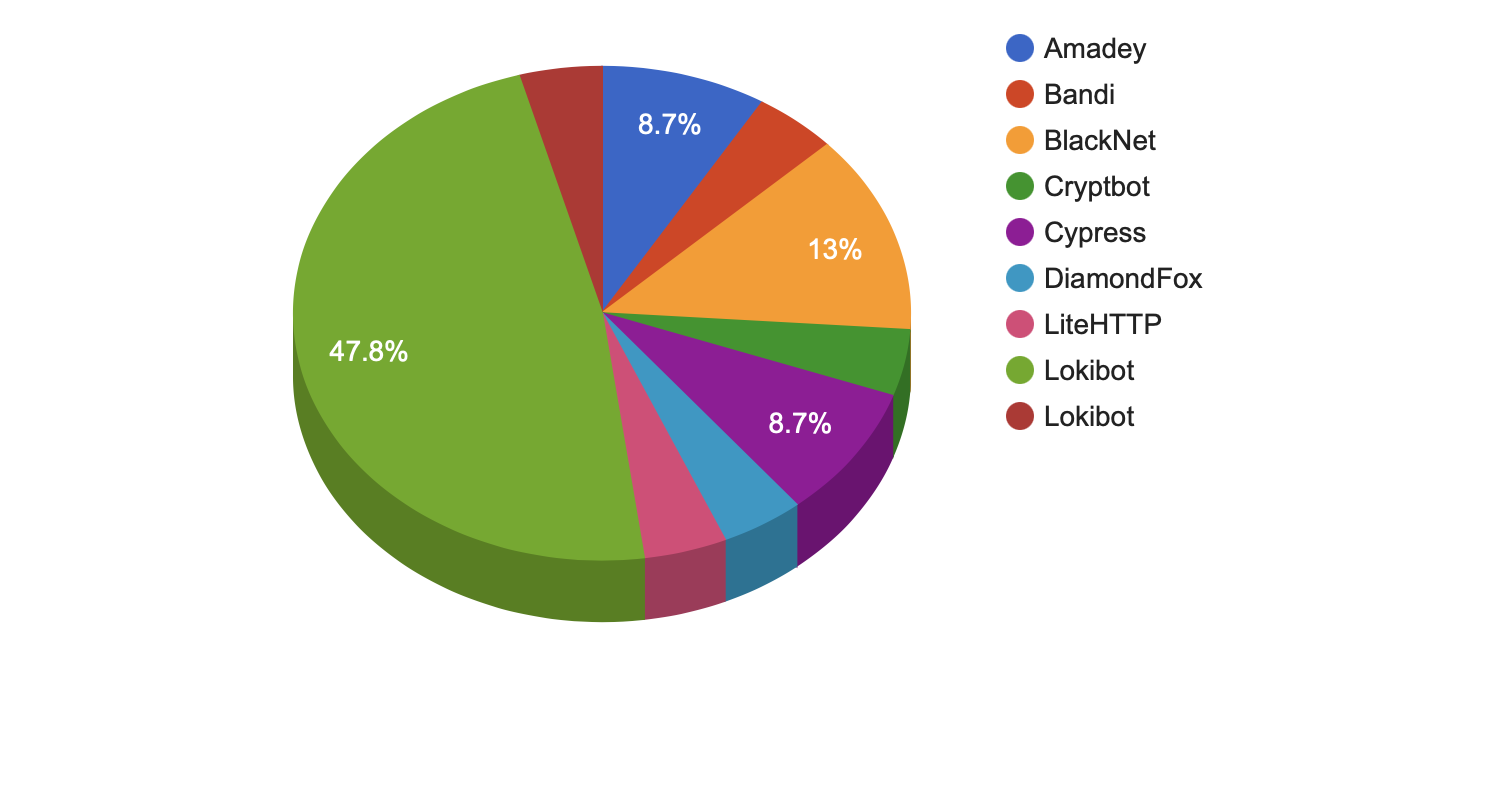
Remote Access Trojan C&C Servers Found
| Amadey |
2 |
176.111.174.249 , 45.153.240.131 |
| Bandi |
1 |
51.255.31.215 |
| BlackNet |
3 |
142.202.136.146 , 173.231.200.9 , 45.133.1.98 |
| Cryptbot |
1 |
47.254.173.53 |
| Cypress |
2 |
178.208.83.27 , 5.23.51.54 |
| DiamondFox |
1 |
8.209.113.52 |
| LiteHTTP |
1 |
80.134.53.98 |
| Lokibot |
11 |
172.67.160.225 , 172.67.189.98 , 172.67.190.183 , 185.208.180.121 , 193.135.12.10 , 193.135.12.12 , 193.142.59.208 , 203.159.80.29 , 31.210.20.58 , 31.41.44.170 , 8.209.68.209 |
| Redirected |
1 |
176.111.174.53 |
Trojan C&C Servers Detected
|
Common Malware
| 9a4b7b0849a274f6f7ac13c7577daad8 |
https://www.virustotal.com/gui/file/c1d5a585fce188423d31df3ea806272f3daa5eb989e18e9ecf3d94b97b965f8e/details |
ww31.exe |
N/A |
Win.Exploit.Shadowbrokers::5A5226262.auto.talos |
| 34560233e751b7e95f155b6f61e7419a |
https://www.virustotal.com/gui/file/8b4216a7c50599b11241876ada8ae6f07b48f1abe6590c2440004ea4db5becc9/details |
SAntivirusService.exe |
A n t i v i r u s S e r v i c e |
PUA.Win.Dropper.Segurazo::tpd |
| b8a582da0ad22721a8f66db0a7845bed |
https://www.virustotal.com/gui/file/5901ce0f36a875e03e4d5e13e728a2724b8eff3c61cc24eb810be3df7508997f/details |
flashhelperservice.exe |
Flash Helper Service |
W32.Auto:5901ce0f36.in03.Talos |
| f37167c1e62e78b0a222b8cc18c20ba7 |
https://www.virustotal.com/gui/file/4647f1a0850a961e341a863194e921c102578a9c4ef898fa5e4b54d9fb65e57b/details |
flashhelperservice.exe |
Flash Helper Service |
W32.4647F1A085.in12.Talos |
| 8c80dd97c37525927c1e549cb59bcbf3 |
https://www.virustotal.com/gui/file/85b936960fbe5100c170b777e1647ce9f0f01e3ab9742dfc23f37cb0825b30b5/detection"target="_blank"rel="nofollow |
Eternalblue-2.2.0.exe |
N/A |
Win.Exploit.Shadowbrokers::5A5226262.auto.talos |
| 34560233e751b7e95f155b6f61e7419a |
https://www.virustotal.com/gui/file/8b4216a7c50599b11241876ada8ae6f07b48f1abe6590c2440004ea4db5becc9/details"target="_blank"rel="nofollow |
SAntivirusService.exe |
AntivirusService |
PUA.Win.Dropper.Segurazo::tpd |
| b8a582da0ad22721a8f66db0a7845bed |
https://www.virustotal.com/gui/file/5901ce0f36a875e03e4d5e13e728a2724b8eff3c61cc24eb810be3df7508997f/details"target="_blank"rel="nofollow |
flashhelperservice.exe |
FlashHelperService |
W32.Auto:5901ce0f36.in03.Talos |
| f37167c1e62e78b0a222b8cc18c20ba7 |
https://www.virustotal.com/gui/file/4647f1a0850a961e341a863194e921c102578a9c4ef898fa5e4b54d9fb65e57b/details"title="https://www.virustotal.com/gui/file/4647f1a0850a961e341a863194e921c102578a9c4ef898fa5e4b54d9fb65e57b/details"target="_blank"rel="nofollow |
flashhelperservice.exe |
FlashHelperService |
W32.4647F1A085.in12.Talos |
|
CVEs with Recently Discovered Exploits
This is a list of recent vulnerabilities for which exploits are available.
CVE-2021-3148
|
An issue was discovered in SaltStack Salt before 3002.5. Sending crafted web requests to the Salt API can result in salt.utils.thin.gen_thin() command injection because of different handling of single versus double quotes. This is related to salt/utils/thin.py. |
9.8 |
03/05/2021 |
03/26/2021 |
CVE-2021-28041
|
ssh-agent in OpenSSH before 8.5 has a double free that may be relevant in a few less-common scenarios, such as unconstrained agent-socket access on a legacy operating system, or the forwarding of an agent to an attacker-controlled host. |
7.3 |
03/05/2021 |
03/26/2021 |
CVE-2021-27886
|
Docker Dashboard Project; Description: rakibtg Docker Dashboard before 2021-02-28 allows command injection in backend/utilities/terminal.js via shell metacharacters in the command parameter of an API request. NOTE: this is NOT a Docker, Inc. product. |
9.8 |
03/01/2021 |
03/09/2021 |
CVE-2021-27730
|
Accellion FTA 9_12_432 and earlier is affected by argument injection via a crafted POST request to an admin endpoint. The fixed version is FTA_9_12_444 and later. |
9.8 |
03/01/2021 |
03/05/2021 |
CVE-2021-25283
|
An issue was discovered in through SaltStack Salt before 3002.5. The jinja renderer does not protect against server-side template injection attacks. |
9.8 |
02/27/2021 |
03/22/2021 |
CVE-2021-25281
|
An issue was discovered in through SaltStack Salt before 3002.5. salt-api does not honor eauth credentials for the wheel_async client. Thus, an attacker can remotely run any wheel modules on the master. |
9.8 |
02/27/2021 |
03/22/2021 |
CVE-2021-2047
|
This vulnerability is in the Oracle WebLogic Server product of Oracle Fusion Middleware (component: Core Components). Supported versions that are affected are 10.3.6.0.0, 12.1.3.0.0, and 12.2.1.3.0. Easily exploitable vulnerability allows unauthenticated attacker with network access via IIOP, T3 to compromise Oracle WebLogic Server. Successful attacks of this vulnerability can result in takeover of Oracle WebLogic Server. |
9.8 |
01/20/2021 |
03/18/2021 |
|
|