Trends
-
The top attacker country was China with 148511 unique attackers (36.89%).
-
The top Trojan C&C server detected was Lokibot with 10 instances detected.
-
The top phishing campaign detected was againts Facebook with 44 instances detected.
The Red Piranha Threat Intelligence team uncovered an intricate cybersecurity attack targeting over eighty Australian businesses. Our team quickly crushed the threat by reverse-engineering the campaign and tools the attacker utilised, allowing them to locate and notify the affected parties swiftly. The cybercriminals used a technique to reject the victim's passwords three times, ensuring they gathered the maximum account of credentials without the user growing too suspicious.
FonixCrypter ransomware gang throws in the towel with MasterKey release
Well known ransomware-as-a-service cybergang FonixCrypter (also known as Xinof) has recently ceased its entire operations, leaving their life of crime behind.
Taking the industry by surprise, they announced via Twitter, that they had “Come to the conclusion we should use our abilities in positive ways and help others.” In addition to apologising to their victims as a sign of good faith, they released their MasterKey, deleted the ransomware source code and closed their Telegram channel, in which they used to advertise their malware campaigns in the dark web.
We recommend that those affected by FonixCrypters ransomware do not use the tool published and instead wait for a tool from an official source to decrypt their files as there is no guarantee that this tool is not in itself malicious.
|
|
|
Top Attackers By Country
| China |
148511 |
36.89% |
| Russia |
118562 |
29.45% |
| United States |
66560 |
16.53% |
| South Korea |
19568 |
4.86% |
| India |
11892 |
2.95% |
| Canada |
8860 |
2.20% |
| Singapore |
6670 |
1.65% |
| Brazil |
6198 |
1.53% |
| Lithuania |
4400 |
1.09% |
| Germany |
3420 |
0.84% |
| Romania |
3173 |
0.78% |
| Czech Republic |
1470 |
0.36% |
| Switzerland |
1245 |
0.30% |
| Peru |
1244 |
0.30% |
| Turkey |
741 |
0.18% |
|
|
|
Top Attackers By Country
|
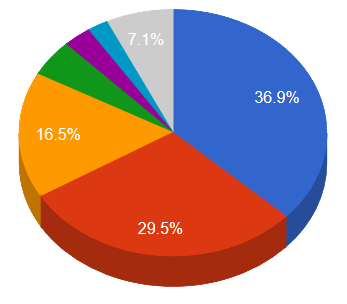 |
 China China Russia Russia United States United States South Korea South Korea India India Canada Canada Others Others
|
|
|
|
|
|
|
|
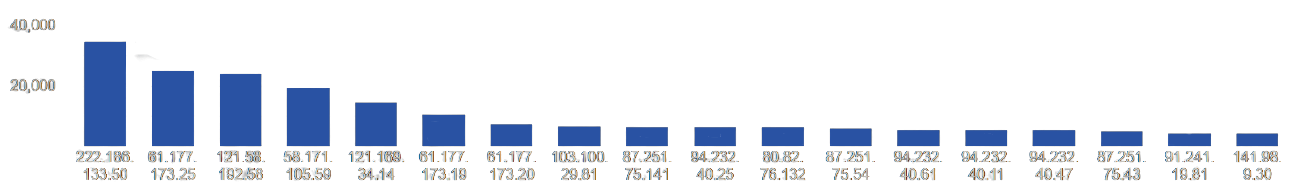
Top Attacking Hosts
| 222.186.133.50 |
34680 |
| 61.177.173.25 |
24880 |
| 58.171.105.59 |
19591 |
| 121.169.34.14 |
14580 |
| 61.177.173.19 |
10704 |
| 61.177.173.20 |
7424 |
| 87.251.75.141 |
6442 |
| 94.232.40.25 |
6396 |
| 87.251.75.54 |
6109 |
| 94.232.40.61 |
5626 |
| 94.232.40.11 |
5454 |
| 94.232.40.47 |
5390 |
| 87.251.75.43 |
5249 |
| 91.241.19.81 |
4439 |
| 141.98.9.30 |
4400 |
|
Top Attackers
 |
|
|
|
Top Network Attackers
| 4134 |
China |
CHINANET-BACKBONE No.31,Jin-rong Street, CN |
| 4766 |
South Korea |
KIXS-AS-KR Korea Telecom, KR |
| 44477 |
Russia |
WELLWEB, NL |
| 202425 |
Netherlands |
INT-NETWORK, SC |
| 207566 |
Russia |
HOSTWAY-AS, RU |
| 209605 |
Netherlands |
HOSTBALTIC, LT |
|
|
|
|
Remote Access Trojan C&C Servers Found
| AgentTesla |
1 |
172.67.217.60 |
| Amadey |
3 |
185.215.113.23 , 45.155.205.65 , 8.208.91.152 |
| Anubis |
1 |
91.203.193.126 |
| Azorult |
4 |
168.119.250.13 , 168.119.251.131 , 170.244.109.73 , 192.210.138.60 |
| Betabot |
1 |
185.222.202.219 |
| DiamondFox |
2 |
35.197.252.30 , 35.198.73.208 |
| DT-Stealer |
1 |
5.79.66.145 |
| Lokibot |
10 |
104.21.37.184 , 104.21.70.230 , 104.223.170.100 , 104.237.252.85 , 185.208.180.121 , 185.212.128.102 , 192.210.138.60 , 195.123.221.253 , 213.227.140.13 , 45.128.207.237 |
| Nexus |
1 |
62.113.112.10 |
| Oski |
1 |
80.78.23.56 |
| Pony |
1 |
45.15.143.189 |
| Predator |
1 |
141.8.192.93 |
| Redirected |
2 |
172.104.159.179 , 172.105.79.146 |
| UAdmin |
1 |
8.209.76.242 |
| Zloader |
1 |
185.240.102.113 |
|
Trojan C&C Servers Detected
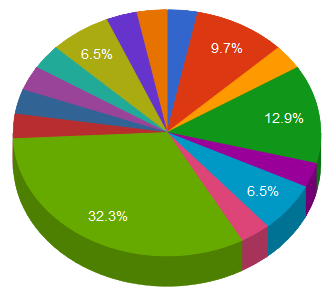 |
 AgentTesla AgentTesla Amadey Amadey Anubis Anubis Azorult Azorult BetaBot BetaBot DiamondFox DiamondFox DT-Stealer DT-Stealer Lokibot Lokibot
|
 Nexus Nexus Oski Oski Pony Pony Predator Predator Redirected Redirected UAdmin UAdmin Zloader Zloader
|
|
|
|
|
|
Common Malware
| 8193b63313019b614d5be721c538486b |
https://www.virustotal.com/gui/file/e3eeaee0af4b549eae4447fa20cfe205e8d56beecf43cf14a11bf3e86ae6e8bd/details |
SAService.exe |
SAService |
PUA.Win.Dropper.Segurazo::95.sbx.tg |
| 34560233e751b7e95f155b6f61e7419a |
https://www.virustotal.com/gui/file/8b4216a7c50599b11241876ada8ae6f07b48f1abe6590c2440004ea4db5becc9/details |
SAntivirusService.exe |
AntivirusService |
PUA.Win.Dropper.Segurazo::tpd |
| 6a7401614945f66f1c64c6c845a60325 |
https://www.virustotal.com/gui/file/b76fbd5ff8186d43364d4532243db1f16f3cca3138c1fab391f7000a73de2ea6/details |
pmropn.exe |
PremierOpinion |
PUA.Win.Adware.Relevantknowledge::231753.in02 |
| 8c80dd97c37525927c1e549cb59bcbf3 |
https://www.virustotal.com/gui/file/85b936960fbe5100c170b777e1647ce9f0f01e3ab9742dfc23f37cb0825b30b5/detection |
Eternalblue-2.2.0.exe |
N/A |
Win.Exploit.Shadowbrokers::5A5226262.auto.talos |
| 9a4b7b0849a274f6f7ac13c7577daad8 |
https://www.virustotal.com/gui/file/c1d5a585fce188423d31df3ea806272f3daa5eb989e18e9ecf3d94b97b965f8e/details |
ww31.exe |
N/A |
W32.GenericKD:Attribute.24ch.1201 |
|
|
|
|
Top Phishing Campaigns
| Other |
970 |
| Facebook |
44 |
| Adobe |
12 |
| Instagram |
3 |
| Google |
12 |
| Microsoft |
5 |
| Amazon.com |
29 |
| Orange |
1 |
| Dropbox |
4 |
| Special |
1 |
| Coinbase |
3 |
| Paypal |
3 |
| Rakuten |
8 |
| Caixa |
2 |
| TSB |
4 |
| Vodafone |
2 |
| Halifax |
1 |
| Apple |
2 |
| Netflix |
2 |
| UniCredit |
1 |
| Playfish |
1 |
| MyMonero |
1 |
|
|
|
|
CVEs with Recently Discovered Exploits
This is a list of recent vulnerabilities for which exploits are available.
CVE-2021-3118
ECSIMAGING PACS 6.21.5 - SQL injection Vulnerability
Medicalexpo
|
Unsupported versions of EVOLUCARE ECSIMAGING (aka ECS Imaging) products through 6.21.5 has multiple SQL Injection issues in the login form and the password-forgotten form. This allows an attacker to steal data in the database and obtain access to the application. |
CVSSv3BaseScore:9.8(AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H) |
01/11/2021 |
01/14/2021 |
CVE-2020-11651
Improper method call validation allows arbitrary code execution vulnerability
Saltstack
|
This vulnerability exists in SaltStack Salt before 2019.2.4 and 3000 before 3000.2. The salt-master process ClearFuncs class does not properly validate method calls. This allows a remote user to access some methods without authentication. These methods can be used to retrieve user tokens from the salt master and/or run arbitrary commands on salt minions. |
CVSSv3BaseScore:9.8(AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H) |
04/30/2020 |
08/19/2020 |
CVE-2020-6207
Missing Authentication Check in SAP Solution Manager
SAP
|
SAP Solution Manager (User Experience Monitoring), version- 7.2, due to Missing Authentication Check does not perform any authentication for a service resulting in complete compromise of all SMDAgents connected to the Solution Manager. ~ |
CVSSv3BaseScore:9.8(AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H) |
03/10/2020 |
03/12/2020 |
CVE-2020-17136
Windows Cloud Files Mini Filter Driver Elevation of Privilege Vulnerability
MicroSoft
|
Microsoft Windows could allow a local authenticated malicious user to gain elevated privileges on the system, caused by a flaw in the Cloud Files Mini Filter Driver. By executing a specially-crafted program, an authenticated attacker could exploit this vulnerability to execute arbitrary code with higher privileges. |
CVSSv3BaseScore:7.8(AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H) |
12/09/2020 |
12/11/2020 |
CVE-2020-1472
Netlogon Elevation of Privilege Vulnerability
Multi-Vendor
|
An elevation of privilege vulnerability exists when an attacker establishes a vulnerable Netlogon secure channel connection to a domain controller, using the Netlogon Remote Protocol (MS-NRPC), aka 'Netlogon Elevation of Privilege Vulnerability'. |
CVSSv3BaseScore:10(AV:N/AC:L/PR:N/UI:N/S:C/C:H/I:H/A:H) |
08/17/2020 |
12/24/2020 |
|
|
|

