Trends- The top attacker country was China with 127557 unique attackers (33.39%).
- The top Trojan C&C server detected was Lokibot with 10 instances detected.
- The top phishing campaign detected was against Facebook accounts with 44 instances detected.
FORTINETOver 500 Australian Fortinet customers including Government agencies and internal departments as well as
iconic organisations within the Australian finance and banking sector, have had their FortiGate IPs and other sensitive credentials leaked on a prominent hacker forum. An unknown hacker posted a list of one-line exploits
for CVE-2019-13379 to steal VPN credentials from vulnerable target devices. These remote command execution vulnerabilities affect over 1.5 million devices globally, and with no automatic update mechanism included within Fortinet's appliance, many affected systems will remain unpatched for the foreseeable future. Additionally, even if the affected Fortinet VPNs are later patched, those passwords can be reused by anyone with access to the leaked data and potentially regain control to the VPNs. Critical summary of CVE-2019-13379: An Improper Limitation of a Pathname to a Restricted Directory ("Path Traversal") in Fortinet FortiOS 6.0.0 to
6.0.4, 5.6.3 to 5.6.7 and 5.4.6 to 5.4.12 under SSL VPN web portal allows an unauthenticated attacker to
download system files via special crafted HTTP resource requests. This vulnerability has been chained with improper permissions set on the SSL VPN session file which can be accessed through path traversal from the Webroot in a publicly disclosedPoC exploit released 11/08/2019.
COVID-19 DOCUMENTATION HACK The European Medicines Agency (EMA) which controls the use of medicines across the European Union, has been a target of a cyberattack. With the attack focusing on documentation relating to the regulatory submission for Pfizer and BioNtech's COVID-19 vaccine candidate BNT162b2. The Agency has launched a full investigation with close cooperation with law enforcement and other relevant entities. No additional information concerning the cyberattack has been released.
GOOGLE PLAY CORE LIBRARY A security flaw has been located within Google Play Core Library, placing hundreds of millions of Android users at risk. The CVE-2020-8913 is a local-code-execution vulnerabilitywhich resides within the SplitCompat.install endpoint in Android's Play Core Library. Thissecurity flaw provides cybercriminals with the opportunity to gain code execution inside popular applications located within the Google Play Store, allowing them to have the same data access as those vulnerable applications.
|
|
|
Top Attackers By Country| China | 127557 | 33.39% | | United States | 109109 | 28.56% | | Russia | 51922 | 13.59% | | India | 26695 | 6.98% | | Netherlands | 18582 | 4.86% | | Canada | 13962 | 3.65% | | Germany | 12896 | 3.37% | | Romania | 4389 | 1.14% | | South Korea | 3253 | 0.85% | | Singapore | 2864 | 0.74% | | Vietnam | 2851 | 0.74% | | Belize | 2608 | 0.68% | | Lithuania | 1524 | 0.39% | | Panama | 1506 | 0.39% | | Bangladesh | 1194 | 0.31% | | Switzerland | 1005 | 0.26% | |
|
|
|
Top Attackers By Country | 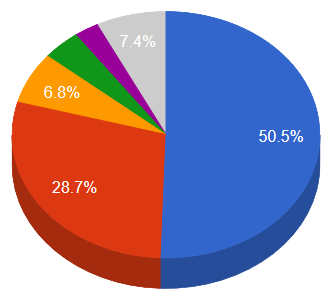 |  China China United States United States Russia Russia India India Netherlands Netherlands
| |
|
|
|
|
|
|
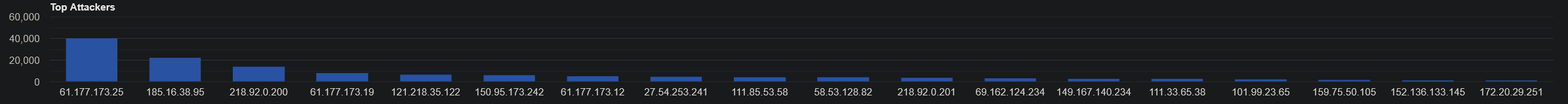
Top Attacking Hosts| 49.88.112.118 | 24330 | | 94.102.51.95 | 15128 | | 218.92.0.208 | 9815 | | 176.9.136.56 | 8393 | | 49.88.112.117 | 6648 | | 121.218.137.15 | 5575 | | 34.200.247.158 | 5491 | | 45.141.84.84 | 4103 | | 49.88.112.115 | 3733 | | 111.85.53.58 | 3032 | | 5.9.16.209 | 2242 | | 193.29.13.27 | 2233 |
|
Top Attackers
 |
|
|
|
Top Network Attackers| 32329 | United States | MONKEYBRAINS, US | | 4134 | China | CHINANET-BACKBONE No.31,Jin-rong Street, CN | | 202425 | Netherlands | INT-NETWORK, SC | | 24940 | Germany | HETZNER-AS, DE | | 14618 | United States | AMAZON-AES, US | | 206728 | Russia | MEDIALAND-AS, RU | | 4837 | China | CHINA169-BACKBONE CHINA UNICOM China169 Backbone, CN | | 42397 | Romania | ***************************************, RO |
|
|
|
|
Remote Access Trojan C&C Servers Found| AgentTesla | 3 | 216.170.126.123 , 45.141.84.146 , 69.174.99.26 | | Amadey | 1 | 148.251.77.71 | | Anubis | 1 | 91.203.193.144 | | AzorUlt | 4 | 185.22.155.185 , 185.244.151.84 , 185.50.25.53 , 95.181.152.221 | | BlackNet | 2 | 141.8.193.236 , 5.226.138.222 | | CobaltStrike | 2 | 188.119.112.174 , 188.119.113.24 | | DiamondFox | 2 | 173.243.112.18 , 8.208.87.35 | | Heodo | 3 | 1.234.65.61 , 172.245.248.239 , 93.148.247.169 | | Keitaro | 2 | 213.226.100.238 , 45.67.229.34 | | Kpot | 2 | 185.22.155.51 , 80.78.22.107 | | Loader | 1 | 8.208.92.202 | | Lokibot | 10 | 103.83.81.68 , 104.223.143.21 , 104.27.167.88 , 137.59.52.154 , 176.118.165.175 , 176.126.200.9 , 185.209.1.14 , 192.185.146.63 , 193.106.175.43 , 95.181.198.117 | | Oski | 2 | 172.67.162.116 , 62.77.159.212 | | Pony | 1 | 137.59.52.154 | | Predator | 3 | 141.8.193.236 , 81.177.165.230 , 81.177.6.221 | | Redirected | 2 | 128.199.97.227 , 139.59.107.195 | | TrickBot | 7 | 13.56.227.131 , 186.47.209.222 , 192.3.73.165 , 3.101.12.202 , 45.12.110.193 , 45.12.110.195 , 45.141.59.212 | | TriumphLoader | 1 | 8.208.13.166 | | Zloader | 1 | 185.240.102.113 |
|
Trojan C&C Servers Detected
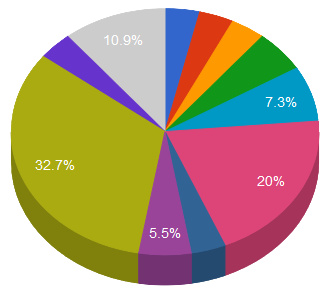 |  AgentTesla AgentTesla Amadey Amadey Anubis Anubis Azorult Azorult BlackNet BlackNet CobaltStrike CobaltStrike DiamondFox DiamondFox Heodo Heodo Keitaro Keitaro Kpot Kpot
|  Loader Loader Lokibot Lokibot Oski Oski Pony Pony Predator Predator Redirected Redirected Trickbot Trickbot TriumphLoader TriumphLoader Zloader Zloader
|
|
|
|
|
|
Common Malware| fb8e3acde54227e3571f5341fafecf31 | https://www.virustotal.com/gui/file/c814e977d6451eeefacce58c0e0ffd395bc8725853a40c67aa7a326d6b39cfe1/details | kmsauto-Downlading.zip | N/A | Win.Tool.Autokms::in01 | | 920823d1c5cb5ce57a7c69c42b60959c | https://www.virustotal.com/gui/file/100318042c011363a98f82516b48c09bbcdd016aec557b009c3dd9c17eed0584/details | FlashHelperService.exe | FlashHelperService | W32.Variant.23mj.1201 | | d5b40faa134ee1e73233e521ac476cdd | https://www.virustotal.com/gui/file/f4c15b1eee06d45fa6115ddcfeb24bdacf54570352e0cb713e1c5895089dae1d/details | 12072020_130241_7399559.xlsm | N/A | W32.F4C15B1EEE-90.SBX.TG/td> | | 8c80dd97c37525927c1e549cb59bcbf3 | https://www.virustotal.com/gui/file/85b936960fbe5100c170b777e1647ce9f0f01e3ab9742dfc23f37cb0825b30b5/detection | Eternalblue-2.2.0.exe | N/A | Win.Exploit.Shadowbrokers::5A5226262.auto.talos | | 2915b3f8b703eb744fc54c81f4a9c67f | https://www.virustotal.com/gui/file/9f1f11a708d393e0a4109ae189bc64f1f3e312653dcf317a2bd406f18ffcc507/details | vid001.exe | N/A | Win.Worm.Coinminer::1201 |
|
|
|
|
Top Phishing Campaigns| Facebook | 44 | | Other | 1777 | | Amazon.com | 32 | | PayPal | 6 | | Virustotal | 1 | | Halifax | 10 | | EE | 1 | | Vodafone | 2 | | RuneScape | 1 | | PayPal | 2 | | Rakuten | 4 | | Google | 1 | | Instagram | 2 | | Microsoft | 10 | | Bradesco | 1 | | TSB | 1 | | Caixa | 2 | | Adobe | 1 | | Special | 1 | | Yahoo | 1 |
|
|
|
|
CVEs with Recently Discovered Exploits This is a list of recent vulnerabilities for which exploits are available. CVE-2020-4006VMware Workspace One Access Command Injection VulnerabilityVMware | VMware Workspace One Access is exposed to a command injection vulnerability in the administrative configurator that could allow a malicious actor with network access to the administrative configurator on port 8443 and a valid password for the configurator admin account to execute commands with unrestricted privileges on the underlying operating system. | CVSSv3BaseScore:7.2(AV:N/AC:L/PR:H/UI:N/S:U/C:H/I:H/A:H) | 11/23/2020 | 12/10/2020 | CVE-2020-17049Microsoft Kerberos Security Feature Bypass VulnerabilitMicrosoft | A security feature bypass vulnerability exists in the way Key Distribution Center (KDC) determines if a service ticket can be used for delegation via Kerberos Constrained Delegation (KCD). To exploit the vulnerability, a compromised service that is configured to use KCD could tamper with a service ticket that is not valid for delegation to force the KDC to accept it. | CVSSv3BaseScore:7.2(AV:N/AC:L/PR:H/UI:N/S:U/C:H/I:H/A:H) | 11/11/2020 | 11/23/2020 | CVE-2020-4463IBM Maximo Asset Management External Entity Injection VulnerabilityIBM | IBM Maximo Asset Management is vulnerable to an XML External Entity Injection (XXE) attack when processing XML data. A remote attacker could exploit this vulnerability to expose sensitive information or consume memory resources. | CVSSv3BaseScore:8.2(AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:N/A:L) | 07/29/2020 | 07/30/2020 | CVE-2020-17140Microsoft Windows SMB Information Disclosure VulnerabilityMicrosoft | Microsoft Windows is exposed to SMB information disclosure vulnerability where an attacker can successfully exploit this vulnerability to access contents of Kernel memory. An attacker could read the contents of Kernel memory from a user mode process. In a network-based attack, an authenticated attacker would need to open a specific file with captured oplock lease, then perform repeated specific modifications to that file. | CVSSv3BaseScore:8.1(AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:N/A:H) | 12/09/2020 | 12/11/2020 | CVE-2020-8913Google Android Play Core Library Arbitrary Code Execution VulnerabilityGoogle | A local, arbitrary code execution vulnerability exists in the SplitCompat.install endpoint in Android's Play Core Library. A malicious attacker could create an app which targets a specific application, and if a victim were to install this app, the attacker could perform a directory traversal, execute code as the targeted application and access the targeted application's data on the Android device. | CVSSv3BaseScore:8.8(AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H) | 08/12/2020 | 08/31/2020 | CVE-2020-1971OpenSSL EDIPARTYNAME NULL pointer de-reference VulnerabilityMutli-Vendor | A null pointer dereference flaw was found in openssl. A remote attacker, able to control the arguments of the GENERAL_NAME_cmp function, could cause the application, compiled with openssl to crash resulting in a denial of service. The highest threat from this vulnerability is to system availability. | CVSSv3BaseScore:7.5(AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:N/A:H) | 12/08/2020 | 12/10/2020 | CVE-2020-9844MacOS Catalina Memory Corruption VulnerabilityApple | A double free issue was addressed with improved memory management. A remote attacker may be able to cause unexpected system termination or corrupt kernel memory. | CVSSv3BaseScore:7.5(AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:N/A:H) | 06/09/2020 | 10/16/2020 | CVE-2020-28914Kata Containers Improper File Permissions VulnerabilityKataContainers | An improper file permissions vulnerability affects Kata Containers. When using a Kubernetes hostPath volume and mounting either a file or directory into a container as readonly, the file/directory is mounted as readOnly inside the container, but is still writable inside the guest. For a container breakout situation, a malicious guest can potentially modify or delete files/directories expected to be read-only. | CVSSv3BaseScore:7.1(AV:L/AC:L/PR:L/UI:N/S:U/C:N/I:H/A:H) | 11/17/2020 | 12/04/2020 |
|
|
|

