| New Threats Detection Added | • WallStealer • ShadowLink |
| New Threat Protection | 122 |
| Newly Detected Threats | 13 |
Weekly Detected Threats
The following threats were added to Crystal Eye this week:
|
Threat name:
|
WallStealer | ||||||||||||||||||
|
WallStealer is a Go-based information stealer that has been active since at least November 2025 and is distributed via infected software files or used by other malware droppers. Similar to other infostealers, once infected, it collects data from web browsers and cryptocurrency wallets, and exfiltrates it via HTTP to the C2 server, with the C2 domain configuration retrieved from a hardcoded Steam user profile.
|
|||||||||||||||||||
|
Threat Protected:
|
04 | ||||||||||||||||||
|
Rule Set Type:
|
|
||||||||||||||||||
|
Class Type:
|
Trojan-activity | ||||||||||||||||||
|
Kill Chain:
|
|
||||||||||||||||||
|
Threat name:
|
ShadowLink | ||||||||||||||||||
|
ShadowLink is a custom command-and-control beacon known to be used in an IoT botnet comprising TP-Link and ASUS routers, and is often paired with MicroSocks to facilitate the creation of a residential proxy network. It has also been observed to be used in the supply chain attack on the ‘xygeni/xygeni-action’ GitHub Action that occurred in March 2026. It has also been observed on Aqua Security’s ‘Trivy-action’, which led to the compromise of several other projects, such as litellm.
The compromises have been linked to the TeamPCP group. Shadowlink is deployed to TP-Link routers by exploiting CVE-2024-21833, which allows unauthenticated command injection from certain network access. The Exploit is used to deploy a custom script which connects the device to the TeamPCP botnet.
|
|||||||||||||||||||
|
Threat Protected:
|
05 | ||||||||||||||||||
|
Rule Set Type:
|
|
||||||||||||||||||
|
Class Type:
|
Trojan-activity | ||||||||||||||||||
|
Kill Chain:
|
|
||||||||||||||||||
Known Exploited Vulnerabilities (Week 3 - April 2026)
For more information, please visit the Red Piranha Forum:
https://forum.redpiranha.net/t/known-exploited-vulnerabilities-catalog-3rd-week-of-april-2026/655.
|
Vulnerability
|
CVSS
|
Description | |||
|
8.8
|
Authenticated RCE - Apache ActiveMQ contains a code injection vulnerability within the Jolokia JMX-HTTP bridge that can allow an authenticated attacker to execute code on the system by sending a crafted discovery URI which can result in the application to load an external configuration file.
|
<= 5.13.9
6.0.0 - 6.2.2 |
5.19.4
6.2.3 |
||
|
8.8
|
Unauthenticated RCE - Microsoft Office Excel contains a vulnerability that can allow an unauthenticated remote attacker to execute code on the system upon opening a specially crafted Excel spreadsheet. This vulnerability affects end-of-life Microsoft products.
|
Check vendor advisory for affected products and versions
|
|||
|
6.5
|
Network Spoofing - Microsoft SharePoint Server contains an improper input validation vulnerability that can allow an unauthenticated attacker to perform network spoofing which may allow an attacker to view sensitive information.
|
SharePoint Server Subscription Edition: 16.0.0 - 16.0.19127.20442
SharePoint Server 2019: 16.0.0 - < 16.0.10417.20114 SharePoint Enterprise Server 2016: 16.0.0 - < 16.0.5548.1003 |
16.0.19725.20210
16.0.10417.20114 16.0.5548.1003 |
||
|
7.8
|
Unauthenticated RCE - Microsoft Visual Basic for Applications (VBA) contains an insecure library loading vulnerability that can allow an unauthenticated remote attacker to execute code on the system upon opening a Microsoft office document from within a directory containing a specially crafted dynamic link library (DLL) file.
|
Check vendor advisory for affected products and versions
|
|||
|
7.8
|
Privilege Escalation - Microsoft Windows contains a privilege escalation vulnerability within Host Process for Windows Tasks that can allow an attacker with local access to elevate to SYSTEM level privileges.
|
Windows 11 24H2: 10.0.26100.1742 - 10.0.26100.7171
Windows 11 25H2: 10.0.26200.6899 - 10.0.26200.7171 Windows Server 2025: 10.0.26100.2033 - 10.0.26100.7171 |
10.0.26200.7392
|
||
|
8.8
|
Authenticated RCE - Microsoft Exchange Server contains an insecure deserialisation vulnerability that can allow an authenticated attacker to execute code on the system.
|
Check vendor advisory for affected products and versions
|
|||
|
7.8
|
Privilege Escalation - Microsoft Windows Common Log File System Driver contains a vulnerability that can allow an attacker with local access to escalate their privileges on the system.
|
Check vendor advisory for affected products and versions
|
|||
|
7.8
|
Unauthenticated RCE - Adobe Acrobat contains a use-after-free vulnerability that can allow an unauthenticated remote attacker to execute code on the system upon opening a specially crafted PDF.
|
Acrobat DC: <= 2020.009.20074
Acrobat 2020: <= 2020.001.30002 Acrobat 2017: <= 2017.011.30171 Acrobat 2015: <= 2015.006.30523 |
2020.012.20041
2020.001.30005 2017.011.30175 2015.006.30527 |
||
|
9.1
|
RCE via SQLi - Fortinet FortiClient EMS contains an SQL injection vulnerability that can allow an unauthenticated remote attacker to execute code on the system via a specially crafted HTTP request.
|
7.4.4
|
7.4.5
|
||
|
8.6
|
Unauthenticated RCE - Adobe Acrobat and Reader contain a prototype pollution vulnerability that can allow an unauthenticated remote attacker to execute code on the system upon opening a specially crafted PDF.
|
Acrobat DC: <= 26.001.21367
Acrobat Reader DC: <= 26.001.21367 Acrobat 2024: <= 24.001.30356 |
26.001.21411
26.001.21411 Windows: 24.001.30362|Mac: 24.001.30360 |
||
Updated Malware Signature (Week 3 - April 2026)
|
Threat
|
Description | |
|
LandUpdate808
|
LandUpdate808 is an exploit kit that makes use of the ClickFix technique to trick users into copy and pasting a malicious payload into PowerShell or a terminal.
|
Ransomware Report |
|
|
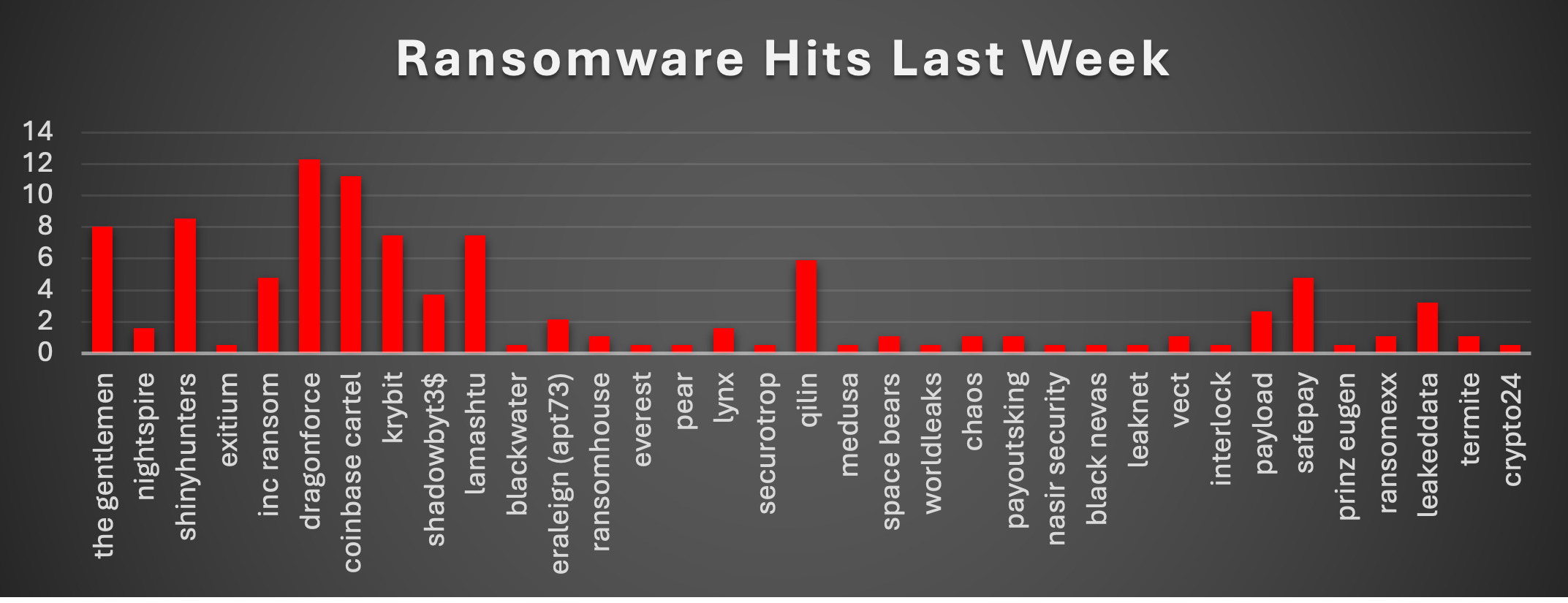
The Red Piranha Team conducts ongoing surveillance of the dark web and other channels to identify global organisations impacted by ransomware attacks. In the past week, our monitoring revealed multiple ransomware incidents across diverse threat groups, underscoring the persistent and widespread nature of these cyber risks. Presented below is a detailed breakdown of ransomware group activities during this period. Ransomware Hits Last WeekRansomware activity this week shows a more distributed threat landscape with multiple dominant actors rather than a single group controlling activity, led by DragonForce at 12.3% and Coinbase Cartel at 11.23%, making them the most active operators this period. They are followed by ShinyHunters (8.56%), The Gentlemen (8.02%), and both Krybit and Lamashtu (7.49%), showing a relatively crowded upper tier of highly active groups. Qilin (5.88%) remains a consistent contributor, while INC Ransom and SafePay (4.81%), along with ShadowBit3$ (3.74%) and LeakedData (3.21%), strengthen the mid-tier activity. Lower-frequency but still relevant groups such as ERALEIGN (APT73), Payload, NightSpire, Lynx, and several actors around 1.07%, including RansomHouse, Chaos, PayoutsKing, Vect, RansomExx, and Termite, contribute to the long tail, while numerous single-incident actors at 0.53% reinforce continued fragmentation across the ecosystem. Overall, the data points to a competitive and decentralised ransomware environment, where activity is spread across several established groups while a broad base of smaller actors continues to sustain ecosystem growth. |
Exitium Ransomware
Exitium is a new, small-volume but data-centric extortion group that emerged on dark-web leak trackers in mid-March 2026 and, during the week under review, publicly claimed one new US healthcare victim - Gastroenterology & Hepatology of CNY, alongside a very large patient-record dataset (167,303 patients, including ~124,000 SSNs). Exitium operates as a double-extortion / “data broker” outfit rather than a disciplined encryption-first crew: only one of its five named victims to date has been described as fully encrypted.
Background and General Description
Origin and First Observation
Exitium first surfaced on public ransomware trackers on 12 March 2026, when FalconFeeds.io announced it was monitoring a new ransomware group named Exitium with two initial victims listed on its Tor portal. Ransomware.live and ransomlook.io subsequently indexed the group, recording a first-discovery date of 17 March 2026 and classifying Exitium as an active data-broker/double-extortion operator. No predecessor, successor, rebrand lineage, or attribution to a known nation-state or established financially motivated syndicate has been reported. No RaaS affiliate program structure has been publicly observed, and no affiliate recruitment posts were identified during the reporting window.
The ransom note - filename YOU ARE UNDER ATTACK.html (alternately rendered YOU ARE UNDER ATTACK!.html) - demands contact within 168 hours (7 days) via Tox, with explicit instruction to download the qTox client from the legitimate GitHub release URL and send a friend request to the group's Tox ID. The note warns against contacting law enforcement, promises data deletion on payment, and declares the group is “not hacktivists and not politically motivated.” RedPacket Security carries a verification banner on every Exitium listing stating the group's victim claims have been reported as including unverified or fabricated victim claims - SOC analysts should therefore treat unconfirmed listings with healthy skepticism until independent evidence (victim notification, dataset release, SEC 8-K) corroborates the compromise.
Tactics, Techniques, and Procedures (TTPs)
Critical Caveat
No independent malware analysis of an Exitium sample has been published by any major vendor (Sophos, SentinelOne, Mandiant, Unit 42, Trend Micro, Kaspersky, ESET, Cybereason, Bitdefender, Microsoft, Cisco Talos, Recorded Future, Intel471, Flashpoint). No public sandbox report exists on ANY.RUN, Tria.ge, or Hybrid-Analysis for a sample tagged “Exitium.” Ransomware.live's own group profile explicitly states that no YARA rules, tools, vulnerabilities, TTPs, or negotiation chats are available for Exitium. Consequently, the TTP table below lists only behaviours directly observed in the ransom note, leak-site posts, or removal-guide writeups. Every entry that cannot be sourced is marked “not publicly available” - none have been inferred.
Analytic Takeaway
Exitium should be treated as a pre-ransom data-exfil actor first, encryptor second. The one confirmed encryption event (Ming Hwei Energy) is the exception; the pattern elsewhere is quiet bulk theft followed by Tor-based naming-and-shaming. Detection investment should therefore skew toward egress anomaly detection, DLP, identity monitoring, and VPN-edge hardening - not solely toward endpoint ransom-note heuristics.
Indicators of Compromise (IOCs)
All IOCs below are verified across at least two independent public sources unless a single-source caveat is noted. Items for which no public IOC exists are listed explicitly as "not publicly available" to prevent speculative blocking.
Infrastructure and Contact IOCs
|
Type
|
Value
|
|
Tor DLS (onion)
|
http://m3ksukzn2glzfdvlusohril7n3iyk4z4fudf6mm22lwhpbpt5aiee5qd.onion/
|
|
Tox negotiation ID
|
0932023CDBDC780B80B4772D22975C9AAD6D1A5921AA4C746C9E4851A307DE1888A6F56FDFBE
|
|
ProtonMail
|
blushaimee@proton.me
|
|
Telegram handle
|
https://t.me/exitiumCORP
|
|
qTox installer (legitimate, referenced by note)
|
https://github.com/TokTok/qTox/releases/download/v1.18.3/setup-qtox-x86_64-release.exe
|
|
Web-server fingerprint
|
gunicorn
|
Host Artefacts
|
Type
|
Value
|
|
File extension on encrypted files
|
.exitium (e.g. 1.jpg.exitium)
|
|
Ransom note filename
|
YOU ARE UNDER ATTACK.html (also YOU ARE UNDER ATTACK!.html)
|
Ransom Note
Crystal Eye 5.5 Mitigation Strategies
Mapping the confirmed (and reasonably-inferred) TTPs onto Crystal Eye 5.5 modules, following the same control-mapping structure Red Piranha uses in its Kazu, Qilin, and Play ransomware threat briefs. Because Exitium's publicly-documented behaviour is dominated by data theft, Tor-based extortion, and Tox C2, the mitigation weight falls on network egress, DLP, identity, and exposure management rather than endpoint-only ransomware heuristics.
Enable SEG anti-phishing, BEC/impersonation detection, DLP on outbound mail; enforce SPF/DKIM/DMARC reject; detonate attachments; on SWG enable DPI + Anti-malware File Scanner on HTTP/HTTPS; subscribe to DNS.Insure blacklist for malicious-domain blocking at DNS tier.
Enforce MFA on all SSL-VPN/WireGuard/OpenVPN via Entra ID SSO (5.5 feature).
Enable CEASR application allowlisting aligned to ASD Essential Eight Maturity Level 3; block execution from %TEMP%, %APPDATA%, %LOCALAPPDATA%\Downloads; activate EDR pre/during/post-execution AV, exploit protection, and ransomware-specific protection; lock USB/CD device control.
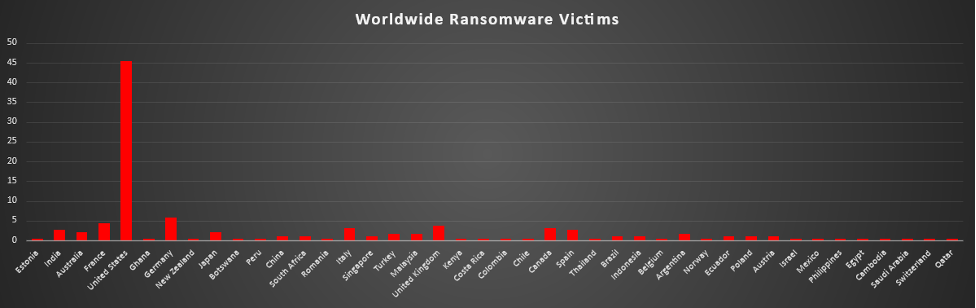
Worldwide Ransomware Victims
This week’s geographic distribution shows continued heavy concentration in the United States, which accounts for 45.45% of all reported ransomware victims, reinforcing its position as the primary target due to financial attractiveness, enterprise density, and high extortion potential.
A second tier of consistently impacted countries includes Germany (5.88%), France (4.28%), United Kingdom (3.74%), and Italy and Canada (3.21%), showing continued focus on developed economies with strong payout potential. Mid-level activity across India and Spain (2.67%), along with Australia and Japan (2.14%), indicates sustained targeting across Asia-Pacific and Europe.
Additional activity in countries such as Turkey, Malaysia, and Argentina (1.6%), combined with a broad set of countries at 1.07% and 0.53%, forms a long tail of opportunistic targeting spanning Latin America, Africa, the Middle East, and Southeast Asia.
Overall, the pattern reinforces a familiar model - ransomware operations remain strategically concentrated in profit-rich regions while maintaining globally distributed execution through broad affiliate-driven campaigns.
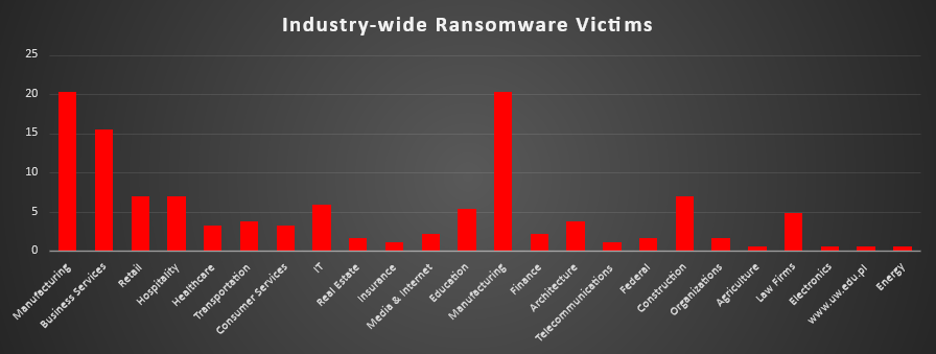
Industry-wide Ransomware Impact
This week’s industry-wise ransomware activity shows continued concentration on operationally critical and revenue-driven sectors, with Manufacturing leading at 20.32%, reinforcing its position as the most targeted industry due to supply chain dependencies and low tolerance for downtime. Business Services (15.51%) follows as a major target, while Retail, Hospitality, and Construction (each 6.95%) show sustained pressure on sectors where disruption can quickly translate into financial loss. IT (5.88%), Education (5.35%), and Law Firms (4.81%) remain consistently targeted due to sensitive data exposure and the likelihood of operational urgency driving ransom payments.
Mid-level activity across Transportation (3.74%), Architecture (3.74%), Healthcare (3.21%), and Consumer Services (3.21%) highlights a broad attack surface across both critical services and commercial sectors. Smaller contributions from Finance and Media & Internet (2.14%), along with Real Estate, Federal, and Organisations (1.6%), indicate continued but lower-volume targeting, while niche sectors such as Insurance and Telecommunications (1.07%), and isolated activity in Agriculture, Electronics, Energy, and other single-incident entries (0.53%), reflect opportunistic attacks.
Overall, the pattern remains consistent - ransomware operators continue to prioritise industries where business disruption creates maximum leverage for extortion and increases the probability of payment.