
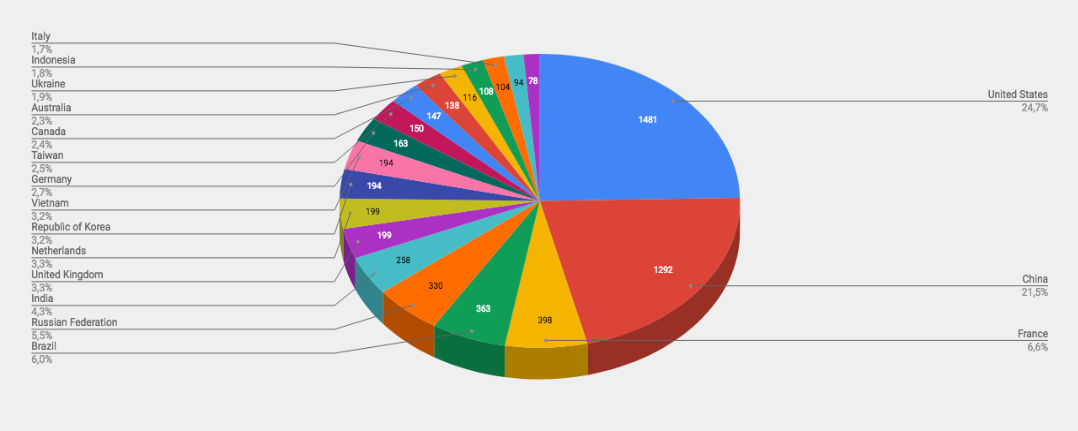
Trends
- United States is on top of the list with 1622 unique attackers (25.3%)
- OTX Pulse was the Top Alarm of the week with 159 occurrences
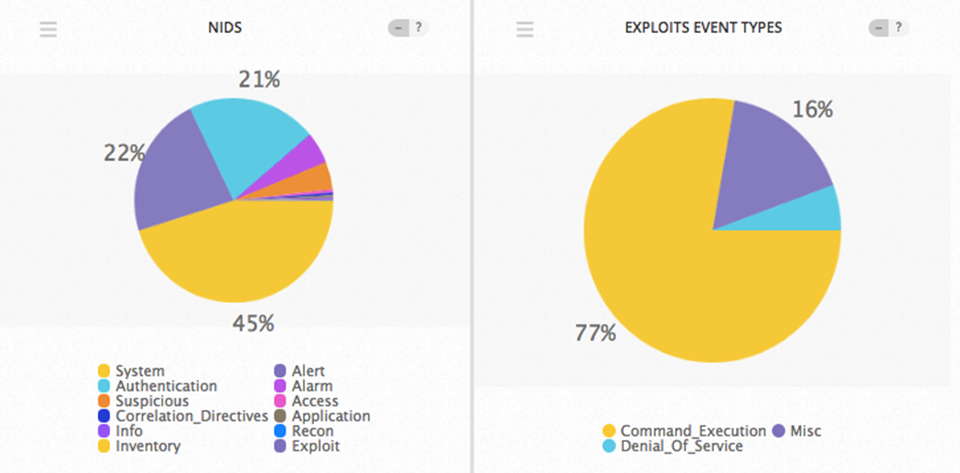
- The exploit event type on top this week was Command Execution with 77% occurrences.
Top Attacker by Country
| Country | No. of Attackers | Occurrences |
|---|---|---|
| United States | 1622 | 25.3% |
| China | 1399 | 21.8% |
| France | 357 | 5.6% |
| Russian Federation | 335 | 5.2% |
| Brazil | 321 | 5.0% |
| United Kingdom | 260 | 4.1% |
| India | 228 | 3.6% |
| Vietnam | 208 | 3.2% |
| Netherlands | 198 | 3.1% |
| Korea | 196 | 3.1% |
| Germany | 192 | 3.0% |
| Australia | 176 | 2.7% |
| Taiwan | 165 | 2.6% |
| Canada | 149 | 2.3% |
| Singapore | 132 | 2.1% |
| Indonesia | 112 | 1.7% |
| Ukraine | 97 | 1.5% |
| Hong Kong | 85 | 1.3% |
| Unknown | 75 | 1.2% |
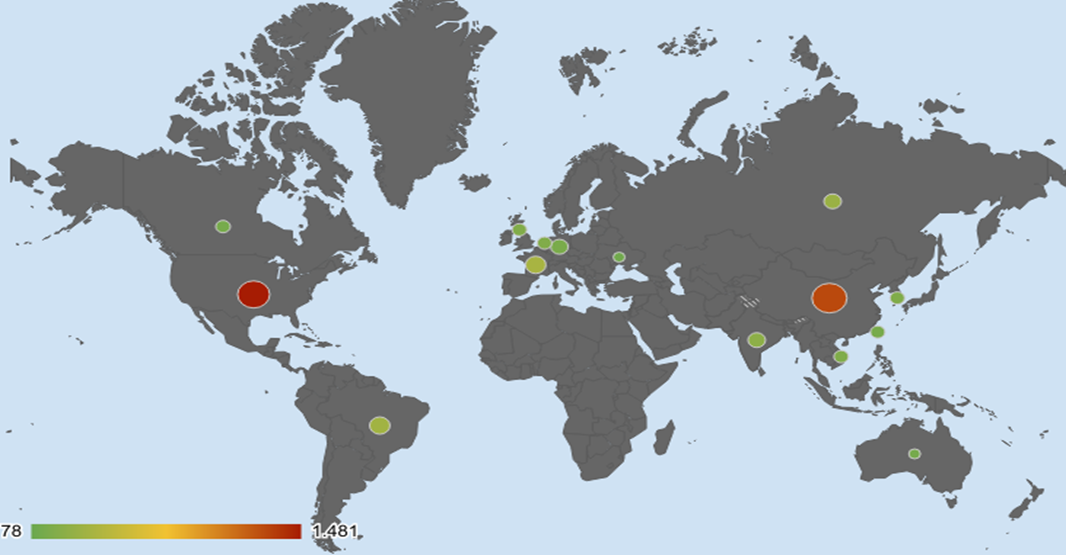
Threat Geo-location
Top Attacking Hosts
| Host | Occurrences |
|---|---|
| 13.107.4.50 | 19 |
| 185.10.68.153 | 17 |
| 185.244.25.165 | 16 |
| 185.244.25.167 | 16 |
| 185.244.25.228 | 16 |
| 117.18.237.29 | 16 |
| 37.48.76.51 | 15 |
| 159.203.169.16 | 15 |
Top Alarms
| Alarm | No. of Occurrences |
|---|---|
| OTX Indicators of Compromise - PULSE | 159 |
| Attack Tool Detected - Attack | 15 |
| Bruteforce Authentication - SSH | 5 |
Comparison from Previous Report
| Alarm | No. of Occurrences |
| OTX Indicators of Compromise - PULSE | 90 |
| Bruteforce Authentication - SSH | 32 |
| Attack Tool Detected - Attack | 1 |
Exploit Event Types and Top Event NIDS
CVE
CVE-2018-20029
The nxfs.sys driver in the DokanFS library 0.6.0 in NoMachine before 6.4.6 on Windows 10 allows local users to cause a denial of service (BSOD) because uninitialized memory can be read.
nvd.nist.gov/vuln/detail/CVE-2018-20029
CVE-2018-1279
Pivotal RabbitMQ for PCF, all versions, uses a deterministically generated cookie that is shared between all machines when configured in a multi-tenant cluster. A remote attacker who can gain information about the network topology can guess this cookie and, if they have access to the right ports on any server in the MQ cluster can use this cookie to gain full control over the entire cluster.
nvd.nist.gov/vuln/detail/CVE-2018-1279
CVE-2018-15800
Cloud Foundry Bits Service, versions prior to 2.18.0, includes an information disclosure vulnerability. A remote malicious user may execute a timing attack to brute-force the signing key, allowing them complete read and write access to the the Bits Service storage.
nvd.nist.gov/vuln/detail/CVE-2018-15800
CVE-2018-15805
Accusoft PrizmDoc HTML5 Document Viewer before 13.5 contains an XML external entity (XXE) vulnerability, allowing an attacker to read arbitrary files or cause a denial of service (resource consumption).
nvd.nist.gov/vuln/detail/CVE-2018-15805
CVE-2018-16635
Blackcat CMS 1.3.2 allows XSS via the willkommen.php?lang=DE page title at backend/pages/modify.php.
nvd.nist.gov/vuln/detail/CVE-2018-16635
CVE-2018-16636
Nucleus CMS 3.70 allows HTML Injection via the index.php body parameter.
nvd.nist.gov/vuln/detail/CVE-2018-16636
