| New Threats Detection Added | • Voidlink • CoGUI |
| New Threat Protection | 155 |
| Newly Detected Threats | 4 |
Weekly Detected Threats
The following threats were added to Crystal Eye this week:
|
Threat name:
|
VoidLink | ||||||||||||||||||
|
VoidLink is a recent malware that is designed for Linux systems as they make up the majority of cloud environments. The malware is written in Zig and uses a different evasion technique based on what Linux kernel the host is running; it automatically chooses to use eBPF or LKM (can do a Hybrid of both as well) depending on the kernel version, this information is sent to the C2 server, which then creates a complied module that is sent back to the infected host. The malware also has the capability to remove all evidence of itself from the infected system; this ranges from deleting logs, command history, artefacts.
The malware can target Docker Containers, Kubernetes, AWS, Alibaba, Tencent and GCP environments. The malware attempts to escape the containers and looks for sensitive files stored on the host system.
|
|||||||||||||||||||
|
Threat Protected:
|
01 | ||||||||||||||||||
|
Rule Set Type:
|
|
||||||||||||||||||
|
Class Type:
|
Trojan-activity | ||||||||||||||||||
|
Kill Chain:
|
|
||||||||||||||||||
|
Threat name:
|
CoGUI | ||||||||||||||||||
|
CoGUI is phishing kit that is primary targeting Japan. The phishing kit deploys a few evasion techniques to avoid detection and analysis. It deploys Geofencing, header fencing and fingerprinting to ensure it’s only accessible but the intended victims. The phishing kit has been identified to be Dracula phishing kit which is link to China.
The campaign has impersonated Amazon, payment cards, transport card, Rakuten, Apple and Japan national tax (NTA). The campaign does not appear to have the ability to capture MFA credentials like similar platforms (evilginx).
|
|||||||||||||||||||
|
Threat Protected:
|
02 | ||||||||||||||||||
|
Rule Set Type:
|
|
||||||||||||||||||
|
Class Type:
|
Credential-theft | ||||||||||||||||||
|
Kill Chain:
|
|
||||||||||||||||||
Known Exploited Vulnerabilities (Week 5 - January 2026)
For more information, please visit the Red Piranha Forum:
https://forum.redpiranha.net/t/known-exploited-vulnerabilities-catalog-5th-week-of-january-2026/635.
|
Vulnerability
|
CVSS
|
Description | |
|
9.8
|
Ivanti Endpoint Manager Mobile (EPMM) contains a vulnerability that can allow an unauthenticated remote attacker to execute operating system commands via HTTP request. Exploitation of this vulnerability can result in an attacker gaining complete access to the system.
|
||
|
9.4
|
Multiple Fortinet products contain an authentication bypass vulnerability that could allow an unauthenticated remote attacker to sign into the device via FortiCloud SSO. Exploitation of this vulnerability required an attacker to have a FortiCloud account along with a registered device and could allow authenticating to devices registered by an account they do not control.
|
Updated Malware Signatures (Week 5 - January 2026)
|
Threat
|
Description | |
|
Tycoon 2FA
|
This is a Phishing-as-a-Service (PhaaS) platform design to bypass/steal 2FA/MFA credentials. The platform uses reverse proxies to intercept traffic between the victim and web page (Man-in-the-Middle). This allows the credentials to be stolen by the hosting platform. The platform primarily targets Gmail and Microsoft accounts.
|
Ransomware Report |
|
|
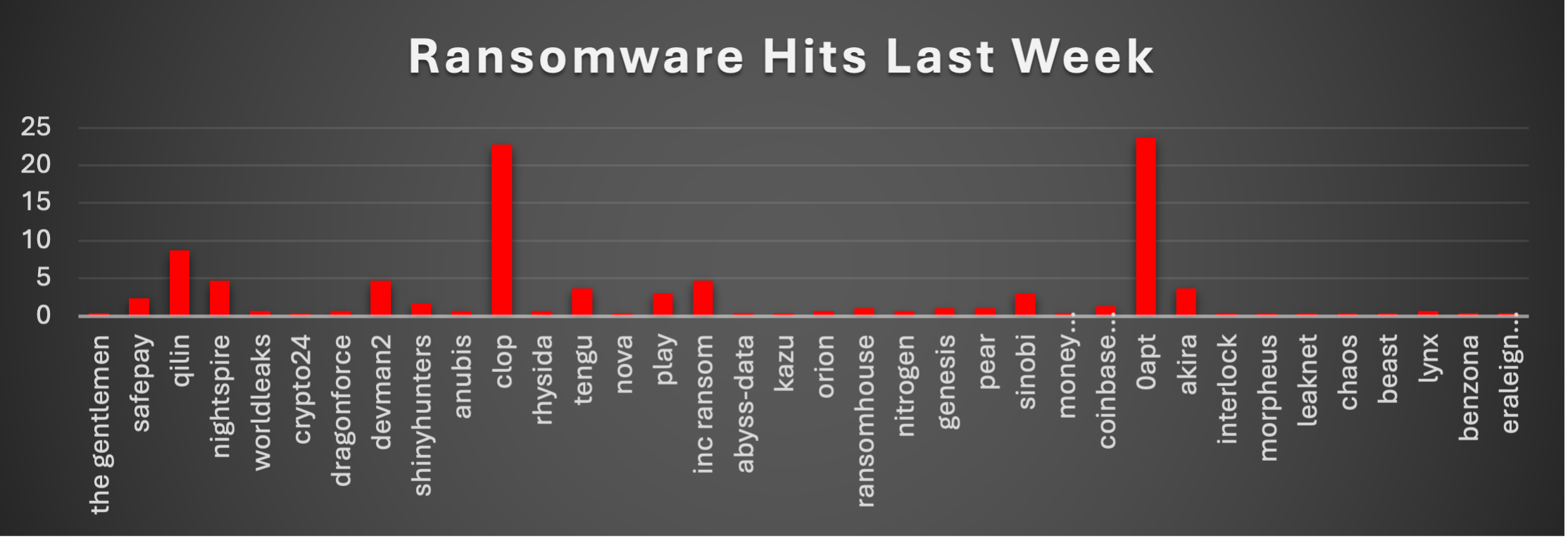
The Red Piranha Team conducts ongoing surveillance of the dark web and other channels to identify global organisations impacted by ransomware attacks. In the past week, our monitoring revealed multiple ransomware incidents across diverse threat groups, underscoring the persistent and widespread nature of these cyber risks. Presented below is a detailed breakdown of ransomware group activities during this period. Ransomware Threat Landscape (Last Week)0APT appeared to dominate this week’s ransomware landscape, claiming responsibility for 23.75% of all reported incidents. However, Red Piranha’s research has determined that 0APT is not a legitimate ransomware group - it is a fake operation relying entirely on social engineering and fabricated claims to extort victims. Its high volume of claimed victims was the result of a bulk dump of fabricated disclosures designed to manufacture credibility, not a genuine campaign. This assessment is detailed further in the 0APT section below Clop followed very closely at 22.74%, forming a powerful upper tier together with Qilin (8.7%). Excluding 0APT’s fabricated claims, Clop and Qilin formed the true upper tier of active ransomware operators this week, together accounting for a significant share of all confirmed activity and underscoring how a small set of high-volume operators continue to shape overall ransomware pressure through aggressive, multi-victim extortion operations. A substantial mid-tier cluster included Nightspire, DevMan2, and Inc Ransom (each 4.68%), Akira and Tengu (each 3.68%), and Play and Sinobi (each 3.01%), with SafePay (2.34%) close behind. This band of actors maintained a steady operational tempo, regularly publishing new victims and contributing a significant secondary layer of risk across multiple regions and industries. Smaller but still persistent operators - such as ShinyHunters (1.67%), RansomHouse, Genesis, and Pear (each 1%), along with Coinbase Cartel (1.34%), and low-mid volume crews like Worldleaks, DragonForce, Anubis, Rhysida, Orion, Nitrogen, Lynx (each 0.67%) - added continuous background noise. While none of them rival the top-tier groups individually, together they meaningfully expand the breadth of active threats. At the long tail, a wide range of fringe brands - The Gentlemen, Crypto24, Nova, Abyss-data, Kazu, Money Message, Interlock, Morpheus, Leaknet, Chaos, Beast, Benzona, Eraleign (APT73) and others (each 0.33%) - appeared only sporadically but still contributed to overall fragmentation and churn. Individually minor but collectively resilient, this long-tail activity highlights how crowded and diversified the ransomware ecosystem remains even in weeks where a handful of families dominate the numbers. |
0APT Ransomware - ASSESSED AS FAKE
0APT presented itself as a newly identified Ransomware-as-a-Service (RaaS) syndicate that emerged on January 28, 2026, claiming to have compromised 71 organisations across multiple sectors within 48 hours. The group claimed to employ double extortion tactics, combining AES-256/Salsa20 file encryption with data exfiltration and public leak threats. However, following in-depth research and analysis, Red Piranha has assessed that 0APT is a fraudulent operation - fake ransomware group that fabricates breach claims to pressure victims into paying ransoms for data compromises that never occurred. The claims, infrastructure, and victim listings are designed to manufacture an illusion of capability rather than reflect genuine technical intrusions.
THREAT ACTOR DESCRIPTION
Group Profile
0APT (pronounced "Zero-APT") presents itself as a financially motivated ransomware syndicate that explicitly distances itself from nation-state Advanced Persistent Threat actors. The group brands itself as a "politically neutral underground syndicate" focused purely on financial gain. Their ransom notes frame attacks as a "tax on security negligence" - psychological tactics designed to normalise payment and discourage victim resistance. Red Piranha’s assessment is that the group lacks genuine ransomware capabilities and instead relies on fabricated breach claims, recycled or publicly available data, and intimidation to coerce payments. All the victims listed on their leak site are assessed as manufactured or unverified claims, not confirmed compromises. Organisations listed by 0APT should conduct their own verification but should not assume a genuine breach has occurred based solely on 0APT’s claims.
Group Characteristics
|
Attribute
|
Details
|
|
Group Name
|
0APT (Zero-APT)
|
|
First Observed
|
January 28, 2026
|
|
Operational Model
|
Fake RaaS
|
|
Extortion Method
|
Claimed Double Extortion
|
|
Motivation
|
Financial
|
|
Victim Count (Jan 28-30)
|
71 claimed
|
RED PIRANHA ASSESSMENT: Red Piranha assesses that 0APT is a fake ransomware group operating purely through social engineering and fabricated breach claims. There is no confirmed evidence of actual ransomware deployment, data exfiltration, or genuine victim compromises. The phishing domains and credential harvesting operations represent the core of 0APT’s actual capabilities - these are social engineering tools, not indicators of a functional ransomware operation. The TTPs below are retained for defensive awareness purposes.
1. Data Leak Site (DLS) Analysis -Fabricated Data
Red Piranha’s internal analysis of the 0APT Data Leak Site (DLS), hosted at oaptxiyisljt2kv3we2we34kuudmqda7f2geffoylzpeo7ourhtz4dad.onion, confirms that the downloadable data offered as “proof” of victim compromises is entirely fabricated. Our findings are consistent with and corroborated by independent analyses from multiple threat intelligence firms.
1.1 Null Bytes and Random Noise
Red Piranha’s inspected the data files from the 0APT DLS revealed that the majority of file content consists of repeating patterns of null bytes. The files contain no meaningful data - no documents, no databases, no credentials, no personally identifiable information.
1.2 Missing File Signatures (No Valid Archive Headers)
Red Piranha’s analysis confirmed that downloaded files do not contain valid ZIP headers or any recognisable file format signatures. Standard archive formats (ZIP, RAR, 7z, TAR) begin with specific “magic bytes” -for example, ZIP files start with PK\x03\x04 (hex 50 4B 03 04). The 0APT files contain none of these signatures.
1.3 Artificially Inflated File Sizes
The 0APT DLS advertises file sizes reaching several terabytes per victim - a volume that would be extraordinary even for established ransomware groups. These sizes are artificially inflated by the streaming random data mechanism. Because the Tor network is inherently slow, an analyst attempting to download and verify a supposed data dump could spend days or weeks downloading what ultimately proves to be meaningless binary noise.
INDICATORS OF COMPROMISE (IOCs)
The following IOCs are associated with 0APT’s observed infrastructure and claimed operations. While the phishing domains and communication channels are confirmed as operational, Red Piranha assesses that 0APT is a fake ransomware group. These IOCs are provided for defensive blocking and awareness purposes. The phishing infrastructure remains a real threat for credential harvesting, even though the ransomware claims are fabricated.
Network Infrastructure
Tor Leak Site
|
Type
|
Value
|
Status
|
|
Onion Address
|
oaptxiyisljt2kv3we2we34kuudmqda7f2geffoylzpeo7ourhtz4dad.onion
|
CONFIRMED
|
|
Site Title
|
0APT | Command Ops
|
CONFIRMED
|
|
Web Server
|
NGINX 1.22.1
|
CONFIRMED
|
Threat Actor Communication Channels
|
Platform
|
Identifier
|
Status
|
|
Tox Messenger
|
AE7FDDF4ADD95AC3DF29802662DA14C51E95A99992E8E087974AFE1A5
7481E5381FE429F8BC8 |
CONFIRMED
|
|
Session Messenger
|
058818f5d84c39403b01ffa023a21b9fe118ffb237fd642c53e73944fb7ac02e6f
|
CONFIRMED
|

Crystal Eye 5.5 (Red Piranha)
- Secure external access (RDP/VPN + apps): Enforce MFA on RDP/VPN, patch exposed apps, block legacy protocols, and apply WAF rules to catch auth bypass / API abuse / injection attempts.
- Privilege management: Rotate admin/MSP credentials, disable unused accounts, enforce least privilege for service accounts (web apps + DB), and monitor privilege escalation inside CE SIEM.
- Execution control + kill-chain correlation: Use CEASR to block unknown binaries executing from %TEMP% / %APPDATA%, restrict PsExec/WMI remoting, and correlate ransomware chains like bcdedit + vssadmin + PsExec, including alerts for AV/service stops.
- Network controls + segmentation: Block known C2/IP/domain indicators, restrict outbound HTTPS to unknown IPs, limit SMB/WinRM east-west movement, isolate admin workstations, and segment AD / file servers / DB servers / critical infra from general user networks.
- Backup hardening + IR playbook automation: Use offline/immutable backups, restrict backup server access, detect shadow-copy deletion attempts, validate restores periodically, and trigger rapid SOAR actions (isolate hosts, block hashes/onion/IOCs, rotate credentials, notify SOC).
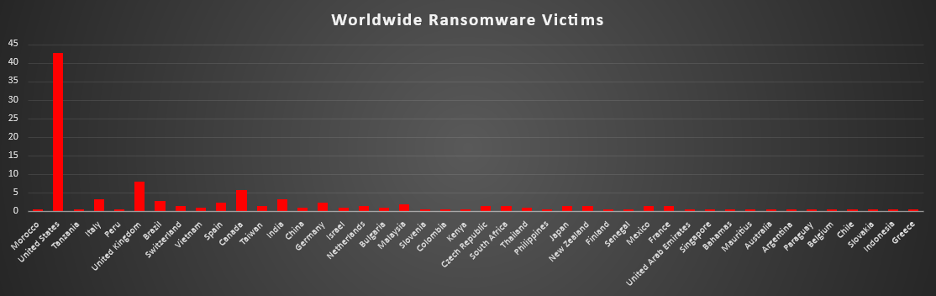
Worldwide Ransomware Victims by Country
The United States remained the primary hotspot for ransomware activity, accounting for 42.65% of all identified victims. That means well over two out of every five known cases this period hit U.S. based organisations, keeping it far ahead of any other single country in terms of observable exposure.
A strong second tier consisted of the United Kingdom (8.06%) and Canada (5.69%), followed by Italy and India (each 3.32%), Brazil (2.84%), and Spain and Germany (each 2.37%). Together, this bloc of mature and large economies forms the bulk of non-U.S. activity, reflecting big digital footprints, consistent incident disclosure, and attractive victim profiles for extortion operators.
A broader mid-band followed, led by Malaysia (1.9%), and a cluster of countries at 1.42% each - Switzerland, Taiwan, Netherlands, Czech Republic, South Africa, Japan, New Zealand, Mexico, France. These figures show that ransomware is firmly entrenched across Europe, Asia-Pacific, and the Americas, not just in North America.
Below that, a long tail of lower-volume geographies - including Vietnam, China, Israel, Bulgaria, Thailand (each 0.95%), and a wide spread of Morocco, Tanzania, Peru, Slovenia, Colombia, Kenya, Philippines, Finland, Senegal, United Arab Emirates, Singapore, Bahamas, Mauritius, Australia, Argentina, Paraguay, Belgium, Chile, Slovakia, Indonesia, Greece (each 0.47%) appeared only sporadically. Individually they contribute small fractions, but collectively they reinforce the pattern: ransomware remains a global problem, touching dozens of countries rather than being confined to a handful of headline markets.
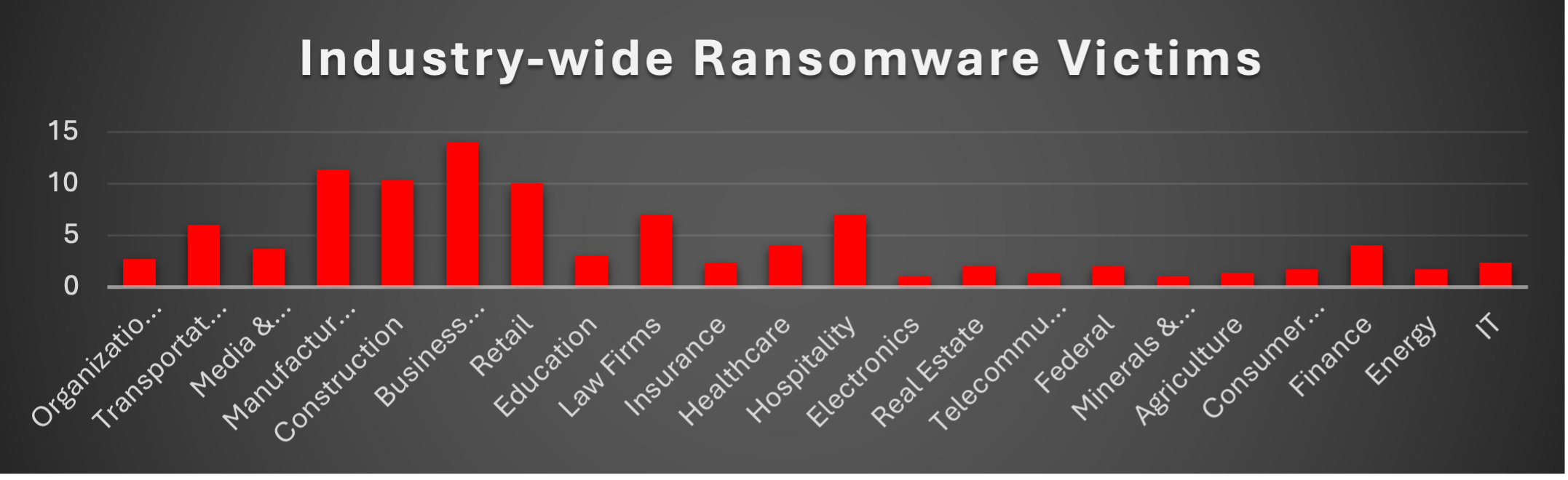
Industry-wide Ransomware Victims
Manufacturing was once again the most heavily targeted sector, accounting for 21.33% of all identified ransomware victims. That puts production environments and supply-chain–critical operations clearly at the top of the risk ladder, where even short outages immediately translate into lost revenue and strong leverage for extortion.
A strong second tier consisted of Construction (11.85%), Business Services (11.37%), and Retail (10.9%). Together, these project-driven, service-oriented and customer-facing industries form a large concentration of cases, reflecting their reliance on time-sensitive projects, logistics, and payment flows that attackers routinely weaponise to force quick decisions under pressure.
A broad mid-band followed, led by Healthcare and Hospitality (each 4.74%), Finance (4.27%), Law Firms and Media & Internet (each 3.79%), along with Education (3.32%), and IT, Transportation (each 2.84%). Supporting this layer, Federal entities and Insurance (each 2.37%), plus Organisations, Consumer Services, and Electronics (each 1.9%), show that both public-sector bodies and information-rich commercial verticals are now routine fixtures in leak-site data rather than exceptions.
Lower-volume but still active categories included Real Estate, Agriculture, and Energy (each 0.95%), with Telecommunications and Minerals & Mining (each 0.47%) forming the long tail. Individually small but collectively meaningful, this spread underlines the same pattern seen across previous weeks: ransomware pressure is highly diversified across industries, and any organisation with digitised operations and monetisable data sits somewhere inside this threat surface.