
Trends
- China is on top of the list with 1397 unique attackers (23.84%)
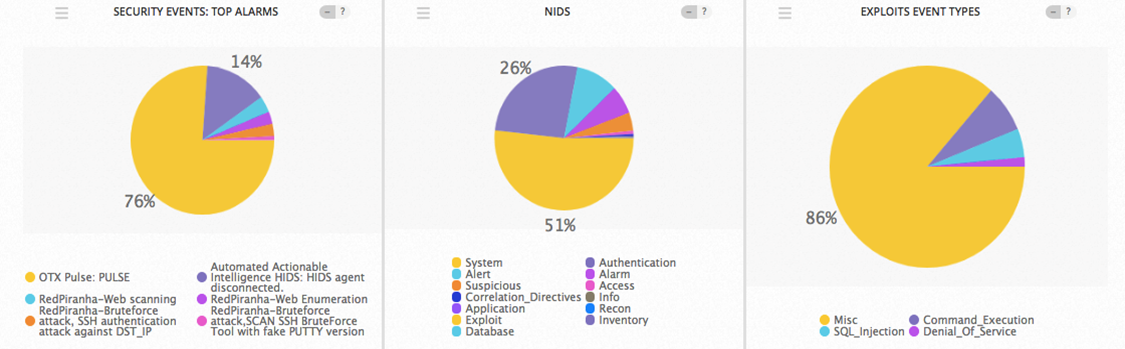
- Bruteforce Authentication was the Top Alarm of the week with 239 of occurrences
Top Attacker by Country
| Country | No. of Attackers | Percentage |
|---|---|---|
| China | 1397 | 23.84% |
| United States | 1137 | 19.40% |
| France | 449 | 7.66% |
| Brazil | 400 | 6.83% |
| Russian Federation | 340 | 5.80% |
| Germany | 248 | 4.23% |
| India | 240 | 4.10% |
| United Kingdom | 201 | 3.43% |
| Republic of Korea | 182 | 3.11% |
| Netherlands | 177 | 3.02% |
| Canada | 153 | 2.61% |
| Vietnam | 137 | 2.34% |
| Taiwan | 130 | 2.22% |
| Italy | 127 | 2.17% |
| Indonesia | 123 | 2.10% |
| Ukraine | 106 | 1.81% |
| Singapore | 91 | 1.55% |
| Poland | 78 | 1.33% |
| Australia | 75 | 1.28% |
| Argentina | 69 | 1.18% |
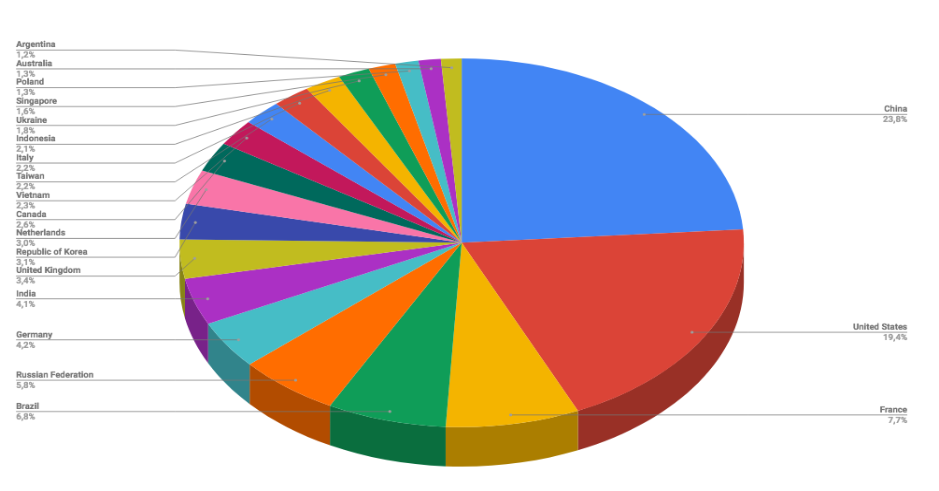
Threat Geo-location

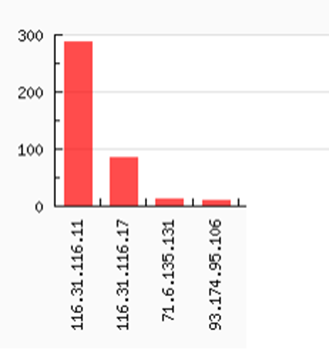
Top Attacking Hosts
| Host | Occurrences |
|---|---|
| 16.31.116.11 | 288 |
| 116.31.116.17 | 86 |
| 71.6.135.131 | 12 |
| 93.174.95.106 | 10 |
Top Alarms
| Alarm | No. of Occurrences |
|---|---|
| Bruteforce Authentication - SSH | 239 |
| OTX Indicators of Compromise - PULSE | 107 |
| Attack Tool Detected - Attack | 8 |
| WebServer Attack - Attack | 3 |
Comparison from Previous Report
| Alarm | No. of Occurrences |
|---|---|
| Bruteforce Authentication - SSH | 201 |
| OTX Indicators of Compromise - PULSE | 88 |
| Database Attack - Stored Procedure - Attack | 14 |
| Attack Tool Detected - Attack | 12 |
| WebServer Attack - Attack | 5 |
| Bruteforce Authentication - Windows Login | 2 |
Exploit Event Types and Top Event NIDS
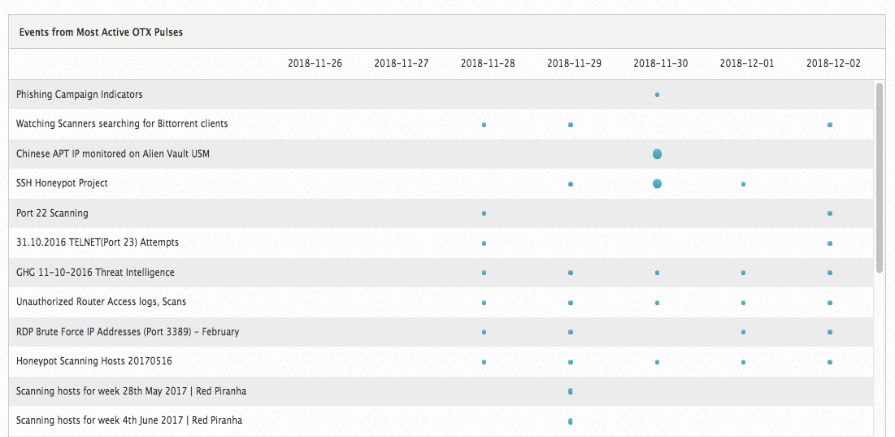
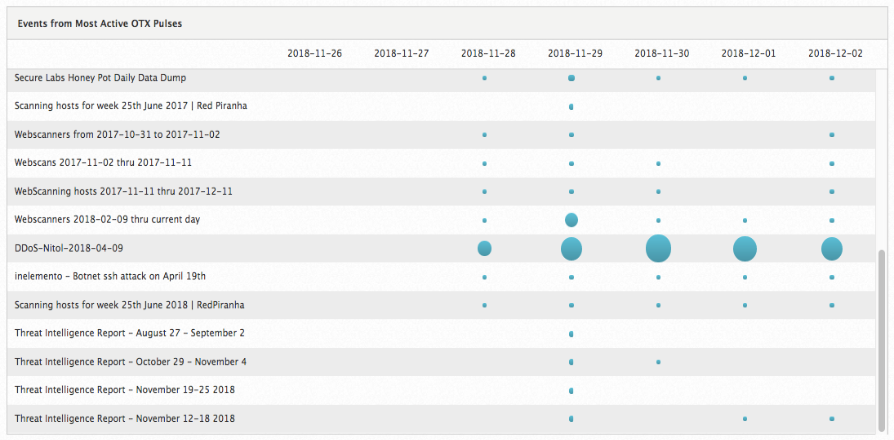
Red Piranha - Open Threat Exchange
| Pulses Subscribed | Indicators | Last Updated | Number of Alarms | Number of Events |
|---|---|---|---|---|
| 6,095 | 892,167 | 2018-12-02 23:05:26 | 6,598 | 7,827 |
Events from the most active OTX
CVE
CVE-2018-19787
An issue was discovered in lxml before 4.2.5. lxml/html/clean.py in the lxml.html.clean module does not remove javascript: URLs that use escaping, allowing a remote attacker to conduct XSS attacks, as demonstrated by "j a v a s c r i p t:" in Internet Explorer. This is a similar issue to CVE-2014-3146.
nvd.nist.gov/vuln/detail/CVE-2018-19787
Vulnerabilities
Details
Category
