
In 2024, the world witnessed an unprecedented surge in ransomware attacks, with LockBit 3.0 leading the charge. According to Red Piranha's 2025 Threat Intelligence & Ransomware Report, LockBit is responsible for 1,462 documented incidents in 2024 alone. This Russia-linked cybercriminal syndicate has not only retained its title as the most active ransomware group but has also redefined the playbook for modern cyber extortion.
Now, lately, the LockBit ransomware group has unveiled its latest version, LockBit 4.0, marking a significant escalation in its cyber warfare capabilities. Designed explicitly to target Linux systems and VMware ESXi infrastructure cornerstones of enterprise and cloud environments, LockBit 4.0 introduces advanced evasion tactics, faster encryption speeds, and a decentralized infrastructure bolstered by redundant Tor-based command-and-control nodes.
Unlike its predecessors, this iteration employs Linux-specific exploits and intermittent encryption techniques, enabling it to bypass traditional detection tools by selectively encrypting file segments while avoiding disruptions to critical system processes.
The group’s shift toward hypervisor and virtual machine attacks underscores a strategic focus on high-impact targets, leveraging misconfigured ESXi interfaces to cripple entire data centers within minutes. With its upgraded infrastructure resilient to takedowns and its payloads optimized for stealth, LockBit 4.0 poses an unprecedented threat.
Operating under a ransomware-as-a-service (RaaS) model, LockBit 3.0 empowers affiliates worldwide to launch devastating attacks while pocketing a cut of every ransom paid. But what fuels its dominance in an era of heightened cybersecurity? How does it evade global law enforcement? And what lessons can organisations learn from its relentless rise?
What Makes LockBit 3.0 the Kingpin of Ransomware?
LockBit 3.0’s dominance isn’t accidental. It’s the result of a calculated fusion of technical sophistication, psychological warfare, and ruthless scalability.
- Military-Grade Encryption: Unlike earlier ransomware strains, LockBit 3.0 employs AES-256 and RSA-4096 encryption algorithms, rendering data irretrievable without the attackers’ decryption keys. Its encryption speed is staggering: a mid-sized corporate network can be fully locked down in under 45 minutes, leaving IT teams with no time to react.
- Double and Triple Extortion: LockBit doesn’t stop at encrypting data. It weaponises stolen information through double extortion, threatening to leak sensitive files on its dark web “leak site” if ransoms (averaging $1.5 million) go unpaid. In high-profile cases, attackers deploy triple extortion by launching DDoS attacks to cripple victims’ online services, amplifying pressure to pay.
- RaaS Affiliate Model: LockBit operates like a Fortune 500 company, offering affiliates (cybercriminals) access to its ransomware toolkit for a 20% commission. This model attracts skilled hackers, including former members of the disbanded Conti gang, who receive tailored variants like LockBit Green. Affiliates are incentivised to maximise profits, creating a self-sustaining criminal ecosystem.
- Omnipresent Targeting: From hospitals delaying critical surgeries to manufacturing plants halting production lines, LockBit’s victims span healthcare, finance, government, and critical infrastructure. Its “spray-and-pray” approach ensures no organisation, regardless of size, is safe.
LockBit Progression: 1.0, 2.0, 3.0, and now 4.0... Continuing
LockBit’s evolution mirrors the rapid advancement of cybercrime itself. Each version introduced game-changing capabilities:
- LockBit 1.0: The prototype focused on speed, using basic encryption to disrupt small businesses. Its simplicity, however, made it easier for defences to detect.
- LockBit 2.0: A quantum leap. The group introduced automated network scanning, enabling affiliates to map out victim infrastructures within minutes. It also added self-propagation features, allowing the ransomware to spread laterally without human intervention.
- LockBit 3.0: The current iteration is a masterclass in innovation. The group launched a bug bounty program, inviting ethical hackers (and rival criminals) to identify vulnerabilities in its tools. This was a move that hardened its malware against reverse engineering. It also introduced intermittent encryption, bypassing detection tools by encrypting files in random chunks rather than all at once.
Operation Cronos: Did Law Enforcement Deliver a Knockout Blow?
In February 2024, a coalition of 10 countries led by the UK’s National Crime Agency (NCA) executed Operation Cronos, a landmark strike against LockBit. In this, authorities:
- Seized 34 servers hosting LockBit’s dark web leak sites and payment portals.
- Froze 200+ cryptocurrency wallets containing over $15 million in ransom payments.
- Arrested three high-ranking affiliates in Poland, Ukraine, and the U.S.
In a bold psychological move, law enforcement hijacked LockBit’s leak site, replacing victim shaming posts with mocking memes and a countdown timer titled “LockBit’s Reign of Terror Is Over.”
The Aftermath: LockBit 4.0 -The Latest Evolution
LockBit resurfaced on a new domain quickly, claiming the takedown was a “minor disruption.”
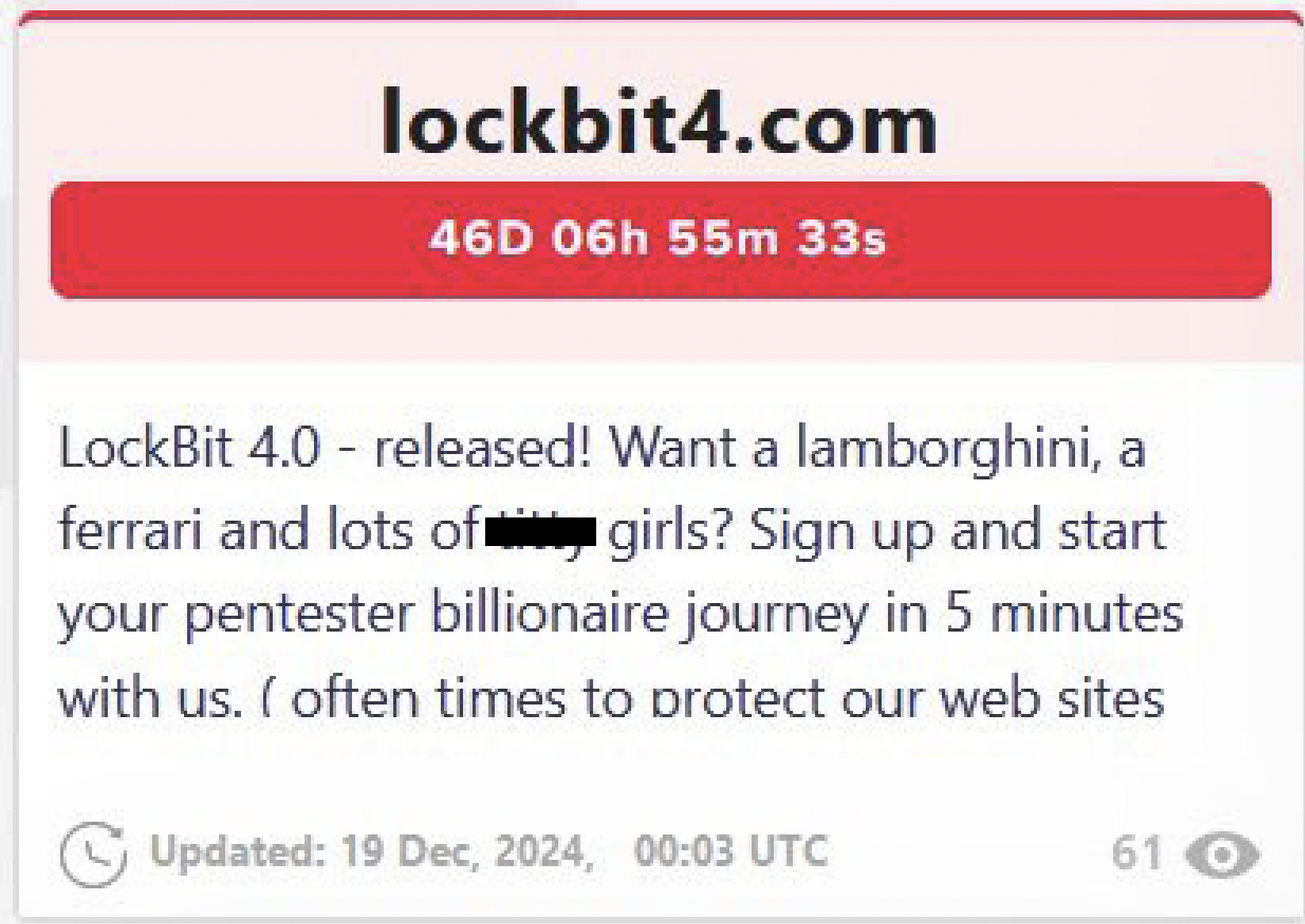
On December 19, 2024, LockBit announced version 4.0 of their ransomware on their dedicated leak site (DLS). This latest iteration represents a significant technical advancement of their malware capabilities, potentially increasing the threat level to organizations.
Concurrent with this release, the group initiated a recruitment initiative for new affiliates, emphasizing their platform's accessibility and potential financial returns. This strategy appears designed to expand their Ransomware-as-a-Service (RaaS) operations and strengthen their position in illicit cyber operations.
What's New with LockBit 4.0?
- Faster Encryption: LockBit 4.0 speeds up its encryption, taking only minutes to lock down big networks. This cuts down the time organizations must respond.
- Better Data Exfiltration: The new version comes with advanced data- exfiltration features, grabbing sensitive info before encrypting it. This lets hackers double down by demanding ransoms for both decryption and keeping the data private.
- Custom Ransom Notes: Hackers can now tweak ransom note templates with LockBit 4.0, tailoring threats to really push victims' buttons.
- Sneakier Than Ever: With better hiding and anti-detection tricks, it’s tougher for security systems to spot and stop this ransomware early on.
- More Perks for Partners: LockBit 4.0 keeps up its Ransomware-as-a-Service (RaaS) gig, offering partners cooler tools, training, and support to help spread the malware.
Standout Features:
-
Targets Anyone: LockBit 4.0 isn’t picky. It’ll go after any industry or organization size, showing off its knack for finding weak spots.
-
Works Everywhere: This ransomware works across multiple platforms, hitting Windows, Linux, and VMware ESXi systems.
-
Tougher Encryption: It uses strong encryption methods that make it nearly impossible to recover data without the decryption key.
Why LockBit 4.0 is a Major Cyber Threat?
LockBit 4.0 marks a big leap in ransomware danger. It dodges defences easily, encrypts data super-fast, and uses complex tactics to shake down victims. All this makes it a tough nut for cybersecurity teams to crack.
The resurgence of LockBit with its 4.0 iteration marks a dangerous leap in ransomware evolution, specifically targeting Linux systems and VMware ESXi environments. A strategic shift toward critical infrastructure often perceived as more secure. Unlike previous versions focused on Windows ecosystems, LockBit 4.0 leverages Linux-specific vulnerabilities and exploits misconfigured ESXi hypervisors, which underpin many enterprise virtualized environments.
This pivot not only broadens its attack surface but also exploits gaps in Linux security postures, which many organizations have historically underprioritized compared to Windows defences. The group’s announcement of LockBit 4.0 coincided with claims of "unprecedented encryption speeds" and enhanced evasion capabilities, signalling a direct challenge to defenders racing to harden cloud and hybrid infrastructures.
Central to LockBit 4.0’s threat is its revamped infrastructure, which now operates across multiple redundant Tor sites and decentralized command-and-control (C2) nodes. This architectural shift complicates law enforcement takedowns and allows attackers to maintain persistence even if parts of their network are disrupted.
Early analyses suggest the ransomware employs intermittent encryption in Linux environments, bypassing detection tools by selectively encrypting file chunks while leaving system processes intact to avoid triggering alarms. Combined with automated lateral movement scripts tailored for ESXi, LockBit 4.0 can cripple virtualized workloads in minutes, holding entire data centres hostage.
Tactics, Techniques, and Procedures (TTPs) and Kill Chain: How Does LockBit Breach Networks?
|
Technique
|
Tactic ID
|
|
Exploit Public-Facing Applications
|
T1190
|
|
Phishing (Spearphishing Links or Attachments)
|
T1566
|
|
Valid Accounts
|
T1078
|
Execution
|
Technique
|
Tactic ID
|
|
Command and Scripting Interpreter
|
T1059
|
|
User Execution
|
T1204
|
Persistence
|
Technique
|
Tactic ID
|
|
Registry Run Keys / Startup Folder
|
T1547.001
|
|
Create Account
|
T1136
|
Privilege Escalation
|
Technique
|
Tactic ID
|
|
Exploitation for Privilege Escalation
|
T1068
|
Defence Evasion
|
Technique
|
Tactic ID
|
|
Obfuscated Files or Information
|
T1027
|
|
Disable or Modify Tools
|
T1562
|
Credential Access
|
Technique
|
Tactic ID
|
|
Credential Dumping
|
T1003
|
Lateral Movement
|
Technique
|
Tactic ID
|
|
Remote Services (RDP, SMB)
|
T1021
|
|
Internal Spearphishing
|
T1534
|
Collection
|
Technique
|
Tactic ID
|
|
Data from Local System
|
T1005
|
|
Archive Collected Data
|
T1560
|
Command-and-Control (C2)
|
Technique
|
Tactic ID
|
|
Encrypted Channel
|
T1573
|
|
Web Service
|
T1102
|
Impact
|
Technique
|
Tactic ID
|
|
Data Encrypted for Impact (Ransomware)
|
T1486
|
|
Data Destruction
|
T1485
|
|
Exfiltration Over C2 Channel
|
T1041
|
LockBit ransomware executes attacks through a seven-stage kill chain aligned with the MITRE ATT&CK framework. It begins with initial access via phishing emails impersonating IT teams, exploiting vulnerabilities in unpatched VPNs (e.g., Fortinet’s CVE-2023-27997), or brute-forcing weak RDP passwords with tools like NLBrute.
Once inside, attackers deploy PowerShell scripts to download payloads and establish persistence by creating hidden admin accounts or modifying Windows Registry keys to auto-start ransomware on reboot.
Next, credential harvesting tools like Mimikatz extract passwords from LSASS memory, enabling lateral movement across networks. Before encryption, LockBit exfiltrates sensitive data (e.g., using Rclone to copy files to cloud storage) to fuel double extortion threats.
The ransomware then encrypts files with extensions like .lockbit3, demanding Monero payments to prevent leaks or DDoS attacks. Attackers pivot laterally via SMB/RDP, exploiting privileges to spread infection, while encrypted C2 channels blend with legitimate traffic to evade detection.
This systematic approach exploiting human error, technical gaps, and encrypted communication demands layered defences: patching vulnerabilities, segmenting networks, monitoring lateral movement, and hardening credentials to disrupt the kill chain before encryption cripples' operations.
Can We Ever Stop LockBit?
While Operation Cronos proved international collaboration can disrupt cybercrime, LockBit’s resilience underscores systemic challenges:
- The RaaS Hydra: For every LockBit affiliate arrested, three new ones emerge. Groups like Black Basta and Play ransomware now adopt “closed” models, operating in secrecy without public leak sites.
- Cryptocurrency Anonymity: Despite tracing tools like Chainalysis, privacy coins like Monero enable untraceable payments.
- AI Arms Race: LockBit affiliates are experimenting with AI-driven phishing tools, while defenders deploy AI-powered threat hunting.
How Red Piranha’s TDIR Solution Detects and Prevents LockBit Ransomware Attacks?
Red Piranha’s Threat Detection, Investigation, and Response (TDIR) solution is engineered to combat sophisticated ransomware threats like LockBit 3.0 through a multi-layered, proactive approach. By integrating cutting-edge technologies with human expertise, the platform addresses LockBit’s evolving tactics from initial network infiltration to data exfiltration and encryption. Here’s how its unique capabilities neutralise LockBit’s threats:
1. Instant 5x Visibility & Behavioural Analytics
LockBit ransomware often evades traditional defences by exploiting zero-day vulnerabilities or blending into legitimate traffic. Red Piranha’s network behavioural analytics provides 5x increased visibility than the other similar solutions across the entire network, endpoints, and cloud environments.
By continuously monitoring east-west traffic patterns, the solution detects anomalies such as unusual lateral movement or spikes in data transfers, the hallmarks of LockBit’s post-compromise activities. For example, if LockBit affiliates use tools like Mimikatz then Red Piranha’s TDIR solution combines behavioural analytics (e.g., detecting LSASS access, rapid file encryption) and machine learning to spot anomalies, while operationalised threat intelligence and Platinum SIEM contextualise alerts.
It supports human-machine teaming with 24/7 SOC access for prioritisation, proactive threat hunting, and forensic log retention (18+ months).
For example, detecting Mimikatz credential theft triggers behavioural alerts, correlates events via threat intel, and escalates to SOC teams for rapid containment, while in-line deployment and multi-tenanted sensors minimise infrastructure changes and TCO, ensuring compliance and end-to-end protection.
2. In-Line Deployment & East-West Traffic Control
LockBit’s affiliates often exploit poorly segmented networks to spread ransomware. Red Piranha’s in-line deployment avoids costly infrastructure changes while enabling granular east-west traffic control. By segmenting the network and applying micro-perimeters, the solution restricts lateral movement, a critical step in containing LockBit’s rapid encryption process. For instance, if an attacker breaches a workstation, the platform isolates the compromised device, preventing ransomware from propagating to critical servers or backups.
3. 24/7 Monitoring & Best-in-Class Detection: Neutralising APTs and CnCs
LockBit’s command-and-control (C2) servers and advanced persistent threat (APT) tactics require round-the-clock vigilance. Red Piranha’s SOC delivers 24/7 monitoring, leveraging AI-driven detection to identify indicators of compromise (IoCs) linked to LockBit’s infrastructure.
The platform correlates threat feeds with network telemetry to spot malicious activities, such as connections to known LockBit C2 domains or anomalous TLS-encrypted traffic patterns. Automated alerts ensure that even stealthy exfiltration attempts like data being siphoned to cloud storage are intercepted before encryption begins.
4. Operationalised Threat Intelligence
LockBit constantly updates its malware to evade signature-based tools. Red Piranha counters this with fully contextualised, automated threat intelligence that integrates real-time data on LockBit’s TTPs (tactics, techniques, procedures), malware hashes, and affiliate infrastructure.
This intelligence is operationalised into the platform, enabling “push-button” deployment of detection rules. For example, if LockBit Green emerges, the system automatically updates its defences to recognise its unique encryption patterns or phishing lures.
5. Proactive Threat Hunting & Forensic Readiness
LockBit operators often linger in networks for weeks before deploying ransomware. Red Piranha’s on-demand threat hunting proactively scours environments for hidden IoCs, such as suspicious PowerShell executions or registry modifications tied to LockBit’s persistence mechanisms.
Red Piranha's Digital Forensics and Incident Response (DFIR) services are designed to enhance incident response cycles effectively. It offers in-depth analysis and remediation strategies to handle breaches, ensuring organisations can quickly recover and restore operations.
Specifically, the DFIR is adept at identifying endpoint-specific issues, such as registry modifications associated with LockBit attacks. This targeted approach ensures precise incident handling and system restoration.
Combined with 18+ months of data retention and integrated PCAP analysis, forensic teams can reconstruct attack timelines, identify entry points (e.g., exploited VPN vulnerabilities), and eradicate dormant payloads before activation.
6. Human-Machine Teaming & SOC Escalation
When LockBit’s encryption begins, every minute counts. Red Piranha’s human-machine teaming merges AI-driven automation with human expertise. For example, if the system detects rapid file encryption (.lockbit3 extensions), it auto-triggers containment protocols (e.g., disabling affected user accounts) while escalating the incident to Red Piranha’s SOC. Analysts then guide responders through evidence-based remediation steps, bypassing the need for costly IR retainers.
7. Vulnerability Management & Compliance
LockBit frequently exploits unpatched software for initial access. Red Piranha’s integrated vulnerability management continuously scans for weaknesses, prioritises critical patches, and ensures compliance with mandates like NIST or ISO 27001. By hardening internet-facing assets and enforcing Zero Trust principles, the solution eliminates the low-hanging fruit LockBit relies on for infiltration.
8. Encrypted Metadata Handling & Data Standardisation
LockBit uses encrypted channels (TLS/HTTPS) to hide C2 communications. Red Piranha’s encrypted metadata analysis deciphers traffic patterns without decrypting content, flagging anomalies like sudden spikes in encrypted traffic to unknown destinations. Meanwhile, data standardisation ensures all logs and alerts are normalised, accelerating threat correlation and reducing false positives.
9. True SOAR & MTD Strategy
Red Piranha’s SOAR (Security Orchestration, Automation, and Response) capabilities execute dynamic Moving Target Defence (MTD) strategies. For example, if LockBit is detected, the platform can automatically rotate credentials, reconfigure firewall rules, or isolate high-risk assets—disrupting the attacker’s control plane and buying time for eradication.
10. Cost Efficiency & Scalability
LockBit disproportionately targets SMEs lacking robust defences. Red Piranha’s single-platform approach reduces upfront costs and operational complexity, making enterprise-grade protection accessible. The solution scales seamlessly, whether defending a small clinic or a multinational corporation, ensuring consistent defence against ransomware.
A Unified Front Against LockBit
Red Piranha’s TDIR solution doesn’t just react to LockBit. It anticipates and dismantles every stage of its attack lifecycle. By combining behavioural analytics, threat intelligence, proactive hunting, and human expertise, organisations can neutralise LockBit’s encryption, extortion, and exfiltration tactics. In an environment where ransomware evolves daily, Red Piranha provides the visibility, speed, and adaptability needed to turn the tide against even the most relentless adversaries.
